The Challenge
Account access management can be a tireless task. Sometimes, people never actually log in their user accounts, and the accounts should be deleted. Others use their access regularly. The struggle is managing access to these accounts in a time-conservative fashion to all of parties involved.
Often times, you spend hours trying to work out the accounts that are out of use so you can disable them. Alternatively, you may set up the accounts to be valid for only a fixed period, and then you need to renew them manually when a partner account has become disabled. This tends to be a more urgent request.
The Solution
By using Windows Logs and SmartResponse™, we can ensure that regularly used accounts stay live. This also ensures that unused accounts expire automatically, without intervention.
The first step is to use AI Engine to create a rule from which you can initiate the process. You only want the alarm firing once a day at the highest frequency. In some scenarios, it make more sense to fire in periods of a week or more.
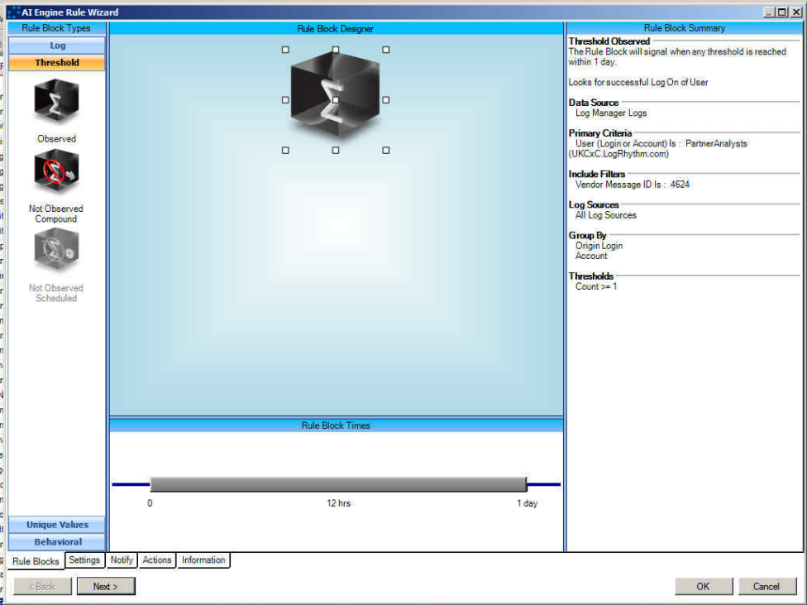
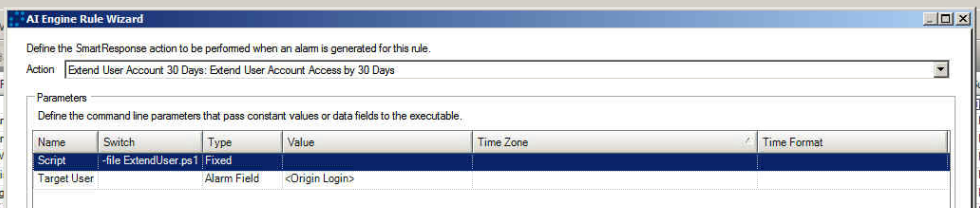
The SmartResponse™ executes a PowerShell script that checks that the user is set to have an expiration time. This is assuming that the case sets the account expiry date to 30 days in the future. It is key to remember that the account your ARM Service is running under must be configured to execute changes on the Active Directory.
How it Works
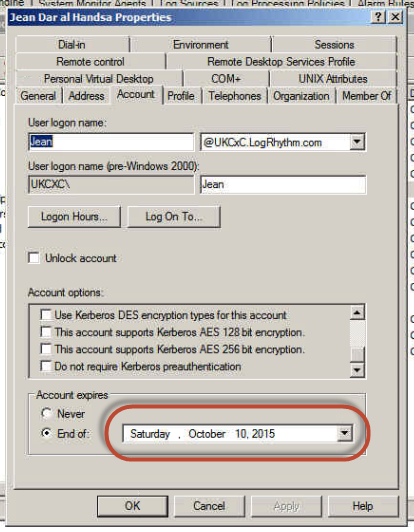
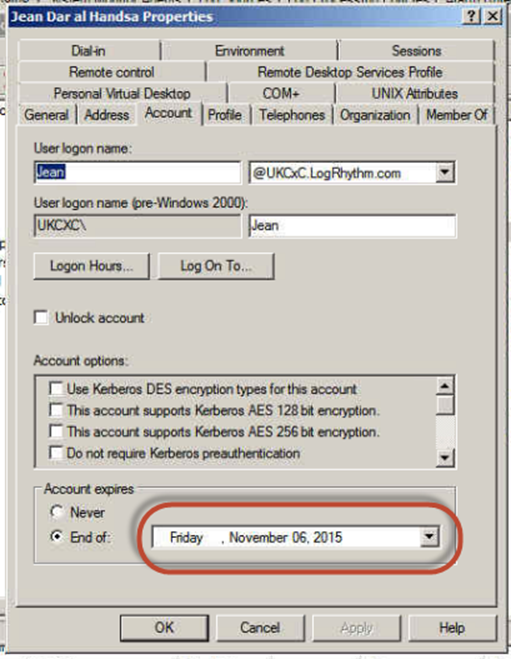
Here is the user in Active Directory:
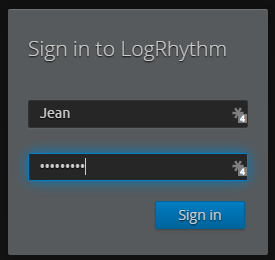
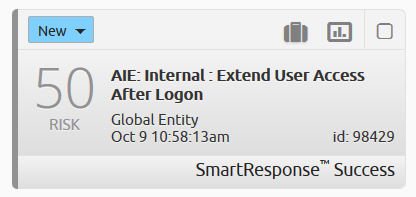
The Alarm triggers and the SmartResponse™ fires:
When you look back in AD, hurrah! You have rewritten the SmartResponse™ so the number of days that the account is extended by 30 days. For configurable action, 30 days may be too short or too long for some scenarios.
Benefit
By automating account termination, you are enhancing the security of accounts that are left unused. Operational automation using LogRhythm’s SmartResponse™ means that unused user accounts are automatically expired, while regularly used accounts continue to be available. This helps enhance the security of your organization, while freeing up your time.