Collaboration between Thomas Hegel and Greg Foss.
For Black Hat this year, Labs decided to try something new and put together a packet capture analysis challenge for the conference. The goal of the challenge was to find the secret launch codes for the fictional company, “Missiles R Us.”
Below, you will find the solution to the puzzle along with details on the Easter eggs hidden throughout.
The PCAP’s Distractions
- Mozilla FTP server browsing and various file downloading
- Streaming of this YouTube video
- Downloading the Dropbox application (not actually using it)
- Uploading of a .txt file containing useless assembly code to 4shared.com
- One post to pastebin.com with the base64 encoding string “so close, yet so far”
- Another pastebin.com post with the string “This is a test…hmmmm”
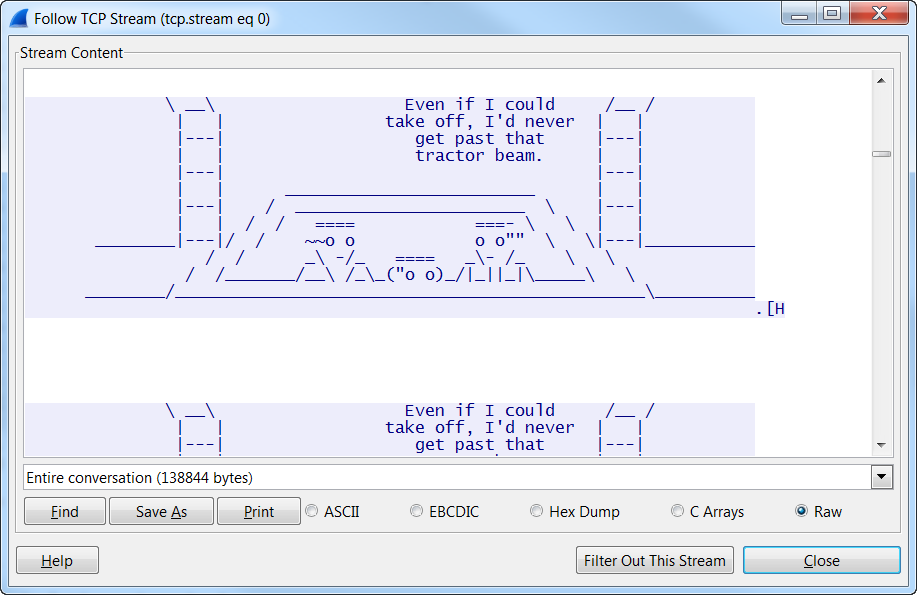
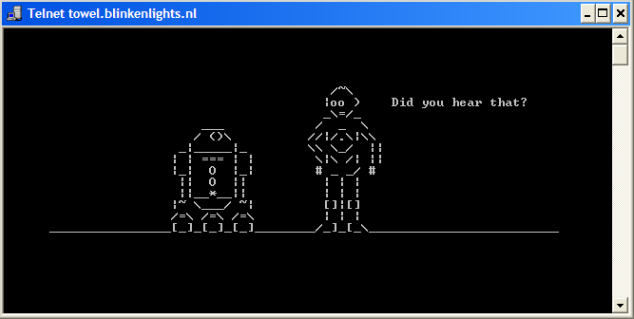
- Using telnet towel.blinklights.nl to play Star Wars over telnet
The Solution
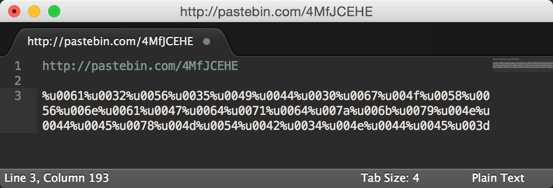
There was one last use of pastebin.com, in particular, to paste a large string of binary text. Following the encoding/decoding trend of the challenge, we must convert that binary to ASCII. Doing so will provide the following string:
JiN4NTM7JiN4NjU7JiN4NjM7JiN4NzI7JiN4NjU7JiN4NzQ7JiN4MjA7JiN4N
GM7JiN4NjE7JiN4NzU7JiN4NmU7JiN4NjM7JiN4Njg7JiN4MjA7JiN4NDM7J
iN4NmY7JiN4NjQ7JiN4NjU7JiN4M2E7JiN4MjA7JiN4MzI7JiN4Njc7JiN4Mz
M7JiN4Mzg7JiN4Mzk7JiN4NjE7JiN4MzM7JiN4MzQ7JiN4MjE7JiN4MzA7Ji
N4MzI7JiN4Mzk7JiN4Mzc7JiN4MjM7
Now we have some base64-encoded data! Decoding that, we get:
Secret La
unch Code:
 2g389a34!
0297#
Getting closer! At this point, we now have a hex encoded string (&#xNN entities to be specific). As the final step, we decode this string to ASCII, and now have the following:
Secret Launch Code: 2g389a34!0297#
Easter Eggs
Hidden throughout the challenge were some Easter eggs. The first of which was basically hidden in plain-sight within a comment field at the bottom of the HTML on the first page.
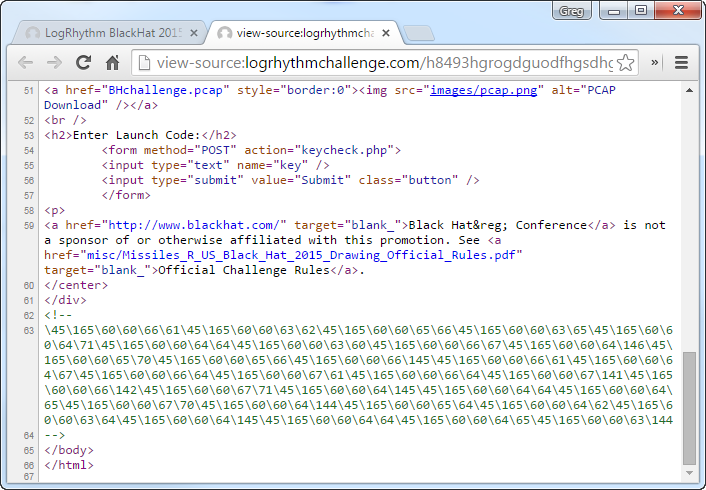
This was another basic encoding challenge, somewhat similar to the actual solution. However, the encoding was a bit different. To reverse this, bring up your favorite encoder/decoder (I like to use http://www.yehg.net/encoding”>http://www.yehg.net/encoding and take this apart. This first string is Octal JavaScript encoded.
\45\165\60\60\66\61\45\165\60\60\63\62\45\165\60\60\65\66
\45\165\60\60\63\65\45\165\60\60\64\71\45\165\60\60\64\64
\45\165\60\60\63\60\45\165\60\60\66\67\45\165\60\60\64\146
\45\165\60\60\65\70\45\165\60\60\65\66\45\165\60\60\66\145
\45\165\60\60\66\61\45\165\60\60\64\67\45\165\60\60\66\64
\45\165\60\60\67\61\45\165\60\60\66\64\45\165\60\60\67\141
\45\165\60\60\66\142\45\165\60\60\67\71\45\165\60\60\64\145
\45\165\60\60\64\64\45\165\60\60\64\65\45\165\60\60\67\70
\45\165\60\60\64\144\45\165\60\60\65\64\45\165\60\60\64\62
\45\165\60\60\63\64\45\165\60\60\64\145\45\165\60\60\64\64
\45\165\60\60\64\65\45\165\60\60\63\144
Once you decode this, you are left with a Unicode string.
Which decodes to base64.
a2V5ID0gOXVnaGdqdzkyNDExMTB4NDE=
Which finally gives you a key…
key = 9ughgjw9241110x41
That, when entered into the scoreboard, does nothing. Its sole purpose is to throw challengers off and send them down a rabbit hole.
In addition to the red herring mentioned above, there was a hidden game that was available if keywords such as “LogRhythm” or “Labs” were entered in to the scoreboard.
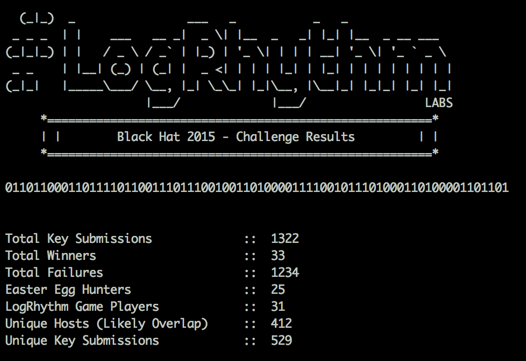
Metrics
Overall, we had a great turnout and want to thank everyone who participated in the game!
Until next year…