When it comes to protecting your organization, the speed that you can detect and respond to a threat is crucial. Measuring the time to detect (TTD) and time to respond (TTR) is nearly equally as important. Capturing and understanding these key performance indicators (KPIs) is vital, because they quantify progress towards goals and help identify areas of improvement.
In the latest release of LogRhythm, we’ve added an awesome feature that automatically generates and reports the TTD and TTR for a resolved incident. Because these KPIs are so valuable and easily seen within LogRhythm, we’ve focused on helping customers get theirs as low as possible. The good news is that there are many ways to streamline your organization’s security operations workflow to achieve a lower TTD and TTR.
Recently, during a customer call, I identified one such occasion. Let’s look at the use case.
An Opportunity to Streamline Workflow
This customer, a large bank, utilizes a SaaS email security solution to scan their inbound email to detect and defend against email-born malware and phishing attacks. While the solution does a great job detecting cyber threats, unfortunately it only provides alerts via email. There is no usable log message* that can be consumed by a NextGen SIEM Platform such as LogRhythm.
Full disclosure, most solutions have a Syslog feed. However, in many cases, the Syslog log source feed doesn’t include anywhere near the wealth of information that email alert provides. The lack of information makes the log an insufficient security source.
Figure 1: Example SaaS Email Alert (Click on images to view larger.)
There are two main risks around relying on an email message to alert on a potential incident. First, an analyst has to monitor an additional interface—another pane of glass. Second, an email notification increases the risk that an important security alert may not be responded to quickly or even missed altogether.
Therefore, I started to think about how this customer could pipe this information directly into LogRhythm. This would help to streamline security operations, which ultimately enables the client to lower and actually measure TTD and TTR.
Lowering Time to Detect and Time to Respond
The first challenge is ingesting the email from the SaaS solution. While it is not a supported log source interface, it is possible to download and consume email from POP, IMAP, or Exchange (on premise or cloud) via the Microsoft Exchange Web Services (EWS) API.
I used a PowerShell script to turn the email alerts from the SaaS provider that match a given subject into text log. Now that the email is in text format, it can be consumed by LogRhythm.
Once LogRhythm was ingesting the malicious email alert from the SaaS provider, I created a custom AI Engine rule to automatically pass on the notification.
Figure 2: LogRhythm Alert for Malicious Email (Click on images to view larger.)
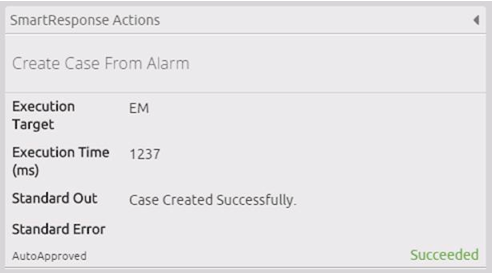
Notice that the AI Engine rule included a SmartResponse™ action that automatically created a case. Case details were also automatically populated, providing instant intelligence and critical details.
Figure 3: Successful LogRhythm SmartResponse (Click on images to view larger.)
At this point, I have been notified by LogRhythm of a potential incident and a new high-priority case has been created. From there, I was able to immediately investigate and respond to the incident. Further search and validation confirmed the user in question didn’t click the email and no breach occurred. Therefore, I closed off the escalated case.
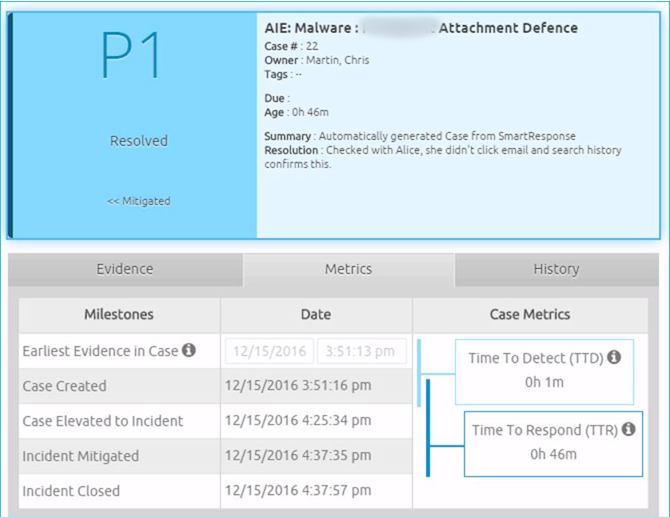
As part of my post investigation process, I can easily see my case KPIs, prominently displayed in the Case Dashboard.
Figure 4: LogRhythm Case Dashboard Displaying TTD and TTR Metrics (Click on images to view larger.)
Results: Streamlined Workflow and Measurable KPIs
In this use case, I was able to streamline operations by consolidating an alert mechanism into a central, seamless end-to-end workflow. By eliminating an additional application that needed to be monitored and automatically piping the alarm information into LogRhythm, I was able to reduce the TTD and TTR, from hours or even days to just minutes.
Furthermore, by managing the workflow through LogRhythm, I was able to track and provide crucial measurement of KPIs that never would have existed had the case been addressed outside the solution. Now I can take those metrics, proudly show them to management, and realistically identify other opportunities for improvement.
To see the LogRhythm SOAR feature set can help you streamline your security operations workflow, watch our on-demand video demo now!