
A Guide to User and Entity Behavior
Analytics (UEBA) Security
You’re facing a constant barrage of threats, some of which you do not even know exist. As the typical point of entry for an attack, users are a difficult vector to monitor and secure. To confront the tidal wave of attacks, you need to hone your attention on users by harnessing the power of user and entity behavior analytics (UEBA).
In this white paper, learn all about UEBA security and how it helps reduce cyber risk by enabling you to respond more quickly to user-based attacks.
Download Your UEBA Guide
Discover everything you need to know about UEBA security
In this UEBA guide, learn the ins-and-outs of what UEBA is and how UEBA security works. Here’s what we’ll cover:
- What users exist in an organization and the risks they pose
- Use cases of user-based threats
- Defending against user-based attacks with holistic analytics
- Differences between deterministic and anomaly analytics
- How LogRhythm UEBA can help your team reduce risk
UEBA security benefits
UEBA security provides security operations centers (SOCs) with visibility to uncover user-based threats that might otherwise go undetected, and the capability to defend against various attacks that range in complexity. Effective UEBA security tools can help:
- Process machine data into a security-relevant schema
- Obtain a true view of users — not just disparate accounts
- Detect and prioritize complex user-based threats
- Accelerate the qualification and investigation of threats
- Streamline response through security operations workflows
When evaluating UEBA security tools, it’s important to keep your top use cases in mind based on your organization’s specific needs and requirements. At a high-level, UEBA security can help you detect and respond to the following UEBA use cases: account compromise, malicious insider threat, and privilege account abuse and misuse.
Protect your environment with UEBA security
Focusing on your users’ activities gives you an important vantage point to identify threats before they become damaging breaches. UEBA security will help you execute with proficiency.
Download Your UEBA Guide
LogRhythm's UEBA approach
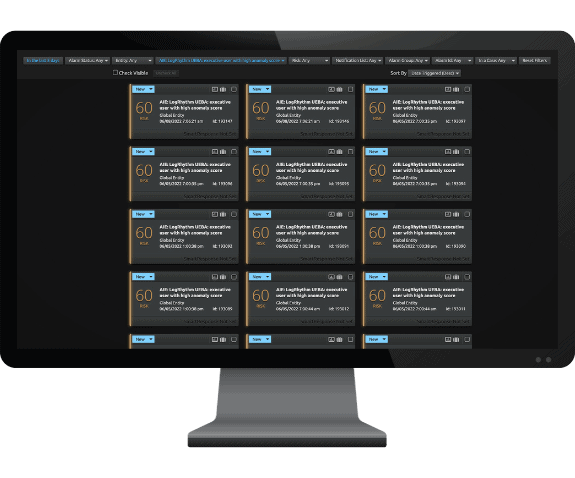
LogRhythm UEBA is LogRhythm’s advanced user entity and behavior analytics solution that helps you identify, qualify, investigate, and remediate threats that might otherwise go unnoticed. It empowers analysts to monitor user behavior, applying both deterministic and anomaly analytics to achieve visibility across a variety of complex threats. LogRhythm UEBA tracks anomalies grouped by the following behavior types:
- Origin hosts
- Impacted hosts
- Authentication classification
- Origin location
- Peer group
In this white paper, you will get a comprehensive breakdown of how LogRhythm UEBA can help you uncover threats to which you were previously blind, giving you the tools to protect your organization and reduce risk.
LogRhythm is Trusted by 4000+ Customers Worldwide
© LogRhythm, Inc. All Rights Reserved.