2024 Cybersecurity Predictions
Posted by: Kelsey Gast
Entering a new year, the cybersecurity landscape is poised for significant shifts, driven by the dynamic interplay between technological advancements and persistent threats. In this blog, industry experts share their insights and predictions, offering a nuanced perspective on the cybersecurity…
Read More
January 9, 2024
LogRhythm SIEM 7.15: Leverage New Beats and Platform Improvements
Posted by: Ryan Gamboa
Getting data into your security information and event (SIEM) instance is crucial, and LogRhythm is highly focused on making it easy to do that. As part of our latest quarterly product release, LogRhythm SIEM version 7.15 builds on the innovation…
Read More
January 4, 2024
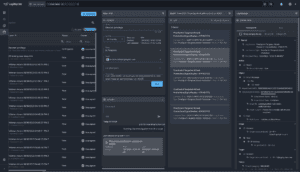
Attain Faster and More Accurate Threat Investigation with LogRhythm Axon’s Single Screen Investigation
Posted by: Josh Feldman
When we built our cloud-native security information and event management (SIEM) platform, LogRhythm Axon, our goal was to make the product as efficient as possible to make the life of an analyst easier. With feature releases every two weeks, we’ve…
Read More
January 4, 2024
Q4 2023 Security Use Cases: Insights From Success Services
Posted by: Moe Hakim
As part of Success Services, this past quarter LogRhythm consultants have been hard at work helping customers improve their defenses against cyberthreats. This quarter, the team observed a shift in attack vectors back into Credential evasion via NTLM, DC manipulation, and…
Read More
January 3, 2024
Optimizing Threat Detection with LogRhythm NDR
Posted by: Derek Watkins
Since we began our quarterly release cycle with LogRhythm NDR, we have been focusing on building a completely new user interface (UI) and introducing new features that help make the life of an analyst easier. Now that we’ve made significant…
Read More
January 3, 2024
Detecting OS Credential Dumping done via WDigest – Security Spotlight
The “Security Spotlight” blog series provides insight into emerging cyberthreats and shares tips for how you can leverage LogRhythm’s security tools, services, and out-of-the-box content to defend against attacks. In this Security Spotlight, we’ll be talking about OS Credential Dumping…
Read More
December 21, 2023