What Comes After Your SIEM Purchase?
Posted by: Kevin D. Kirkwood
Let’s say you recently acquired a security information and event Management (SIEM) solution and now have a new layer of defense in the war against cybercriminals. Check! You’re done right? Not even close. The reality is there is still a LOT more…
Read More
July 24, 2023
Guide to Building a Cybersecurity Incident Response Plan [Part 2]
Having a cybersecurity incident response plan is essential for any organization that wants to be prepared for a security incident. By being prepared for an incident, your organisation is able to align and respond quickly if and when one happens.…
Read More
July 17, 2023
Detecting Microsoft Exchange Zero-Day Exploits
Posted by: Brian Coulson
What is a Zero-Day Exploit? What Can be Done About Them? In cybersecurity, a zero-day exploit refers to the method a hacker uses to take advantage of a security vulnerability in a computer system, software, or network. When a zero-day…
Read More
July 16, 2023
Guide to Building a Cybersecurity Incident Response Plan [Part 1]
Cybersecurity incidents are a fact of life in today’s digital world. Every day, organizations of all sizes are targeted by hackers and other cyber criminals. In 2022, there were over 600 billion cyberattacks worldwide, and the number is only expected…
Read More
July 10, 2023
Improving the SOC Analyst Experience
Posted by: Kelsey Gast
It’s essential to continuously improve the analyst experience (AX) and maximize the team’s efficiency when protecting the organization. Focusing on what matter the most to security analysts and making their job easier can also reduce burnout and help you retain…
Read More
July 7, 2023
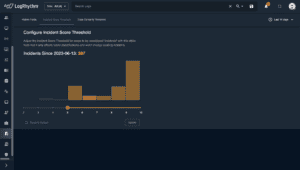
Gain Greater Efficiency in Detecting Threats with LogRhythm NDR
Posted by: Derek Watkins
We’re always working to improve and expand our LogRhythm NDR functionality to better suit our customers’ requirements. Last quarter, we finished overhauling our User Interface (UI) to ensure that traffic anomalies that signal malicious activity surface quickly and that information…
Read More
June 29, 2023