Using the MITRE ATT&CK Framework to Boost Ransomware Defenses.
Two variants of Ransomware as a Service (RaaS) – REvil and Conti – are behind some of the most widespread and successful cyberattacks today.
Don’t let these ransomware attacks siege your operations. Download this white paper to learn how to use the MITRE ATT&CK Framework to improve your security posture, plus discover insightful tactics, techniques, and procedures (TTPs) used by REvil and Conti.
Get Your Ransomware Guide Today
What’s inside our MITRE ATT&CK ransomware guide
Zeroing in on REvil and Conti, MITRE ATT&CK provides useful information about the TTPs used by these ransomware strains. You’ll gain key insight into techniques such as:
- T1486: Data Encrypted for Impact
- T1490: Inhibit System Recovery
Don’t miss your chance to discover best practices for detecting and responding to these tactics. In this guide, cybersecurity experts will walk you through several examples in detail!
How MITRE AT&CK can help you detect ransomware
The techniques listed in the MITRE ATT&CK Framework can help you better understand what normal activity looks like in your environment and spot lateral movement, abuse of privileged accounts, and suspicious process executions.
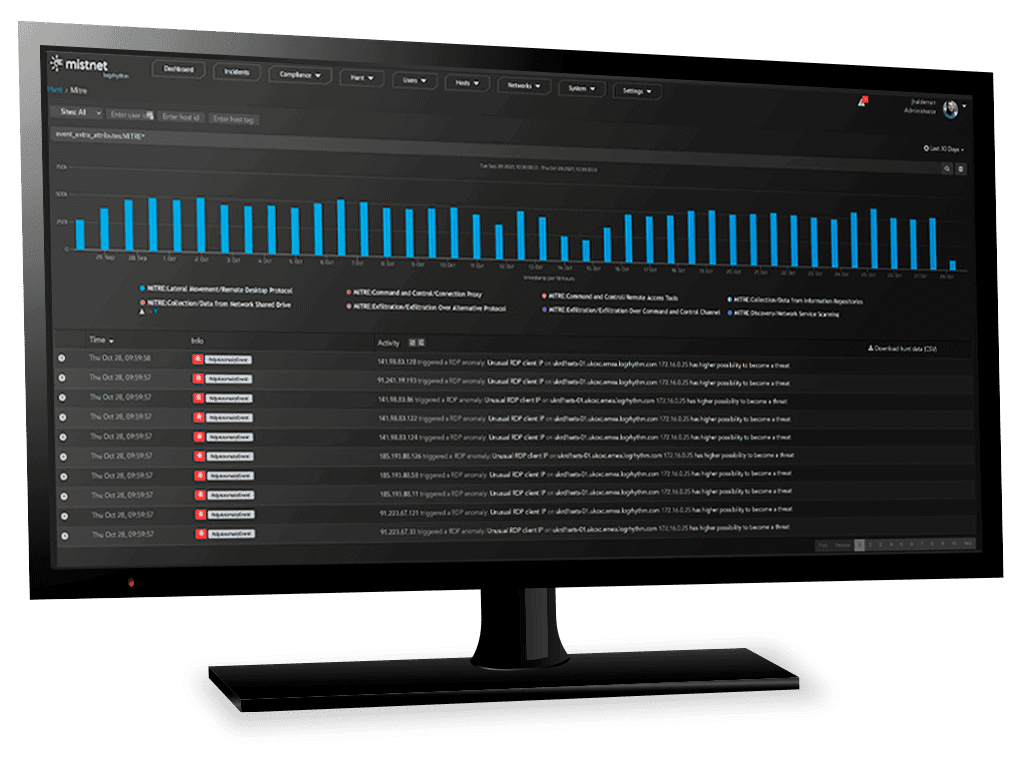
Detecting ransomware activity with LogRhythm
The LogRhythm Labs team is dedicated to building ATT&CK into the LogRhythm SIEM Platform to ensure comprehensive, up-to-date, and verifiable threat detection.
By building detections based on the TTP details from MITRE ATT&CK within your own monitoring or detection and response platform, you will be able to detect the documented techniques, as well as activity that is suspicious and could lead to malicious activity sooner rather than later.
This paper focuses on how you can use ATT&CK to enhance, analyze, and test your threat detection efforts. Let’s dive in!
LogRhythm is trusted by 4000+ customers worldwide
© LogRhythm, Inc. All Rights Reserved.