The “Security Spotlight” blog series provides insight into emerging cyberthreats and shares tips for how you can leverage LogRhythm’s security tools, services, and out-of-the-box content to defend against attacks.
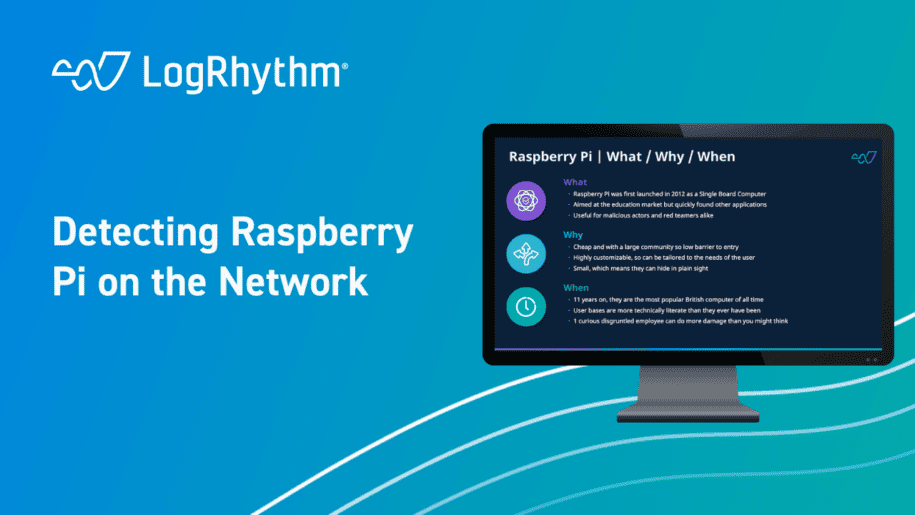
In this Security Spotlight, we’ll be talking about the Raspberry Pi, their value on both sides of the hacking paradigm, and how to detect them on your network.
What Is the Raspberry Pi?
For those unfamiliar with it, the Raspberry Pi made its debut in 2012 as an affordable single-board computer system. It was initially designed to be used as an educational tool in schools looking to enhance their computer science lessons. However, it quickly expanded beyond that initial scope and gained popularity in various other fields, including robotics and, most notably for us, hacking.
The Raspberry Pi proves valuable to attackers and is frequently employed by red teamers seeking to improve their skills and demonstrate to their customers just how quickly they can infiltrate an organization’s network.
Why Should You be Looking Out for Raspberry Pi’s?
Raspberry Pi’s are comparatively cheap, meaning that from a fiscal perspective, there is a low barrier to entry. When coupled with the abundance of online resources, including dedicated communities and educational guides, this significantly increases the ease with which an aspiring hacker can put them to use.
For people with malicious intent or red teamers aiming to demonstrate their worth, the platform offers extensive customization options, allowing it to be tailored to suit the needs of the user. Finally, its compact size makes it incredibly easy to conceal in plain sight. In fact, it’s not uncommon for red teamers to deploy Raspberry Pi’s on corporate networks for extended periods, spanning days or even months, without detection. This can hold true even when the devices are not being employed for malicious purposes.
Eleven years since its launch, the Raspberry Pi and all of its derivatives have become the most popular British computer to ever be sold. However, due to the ongoing global chip shortages, obtaining these devices is certainly not easy.
While it’s true that education is one of the most challenging parts of cyber security, it’s equally true that user bases are now more technically literate and savvy than ever before. The potential for insider threat activities becomes a tangible concern when we realize that all it takes is a single disgruntled employee with a curious mind who decides to explore using a Raspberry Pi for malicious purposes.
How Can LogRhythm Help You?
The Analytic Co-Pilot team has established a simple log observation rule block designed to identify known MAC addresses that are registered to Raspberry Pi devices. It’s important to note that this may not detect advanced users who have spoofed a different MAC address. However, for the typical disgruntled employee, such advanced techniques are unlikely to be employed.
By ingesting Microsoft Dynamic Host Configuration Protocol (Microsoft DHCP) logs, we can look for the MAC of the devices connecting to the network, and then flag when the device MAC matches the identified patterns. The Raspberry Pi Foundation has included additional MAC addresses in their range since this rule was created, which can be added by following the same basic regex formula the Co-Pilot team used in this rule.
For more information on how to enable these rules within your LogRhythm deployment, check out our community page to read more, download, and then import the rule into your platform.
For other Security Spotlight episodes, you can access the full playlist here.