Cloud Security Monitoring
Eliminate cloud security complexity with unified visibility and threat detection
Software-as-a-service (SaaS) applications and self-hosted cloud infrastructure are transforming IT. But while the cloud unlocks new value for your business, it also creates complexity and challenges for your security team. Sensitive data is now in more locations than ever, and every cloud provider has a unique approach to security. Meanwhile, the rapid pace of change that the cloud enables makes cloud security a continuously moving target.
LogRhythm Axon is a cloud-native security information and event management (SIEM) that brings security visibility and threat detection for SaaS applications, self-hosted cloud resources, and traditional on-premises infrastructure together into a unified set of views and security operations workflows. This makes it easy to manage your cloud security posture holistically and detect and respond to threats more effectively.
LogRhythm Axon unifies your cloud security monitoring.
The same dynamic attributes that make cloud applications and infrastructure so valuable also make it challenging for your security team to keep pace. Applications, users, and self-hosted cloud assets often appear and disappear daily through fast-moving DevOps processes. Meanwhile, the number of different SaaS and cloud providers in use just keeps multiplying.
Most SaaS and cloud providers have extensive security policies and logging capabilities. The problem is that each approaches security in a slightly different way, leaving your security team with silos of data that can’t be analyzed in a consistent way.
LogRhythm Axon collects, normalizes, enriches, and analyzes security signals from your SaaS applications, cloud infrastructure providers, and on-premises infrastructure through a unified security approach.
This takes the complexity out of cloud security monitoring and empowers your security team with:
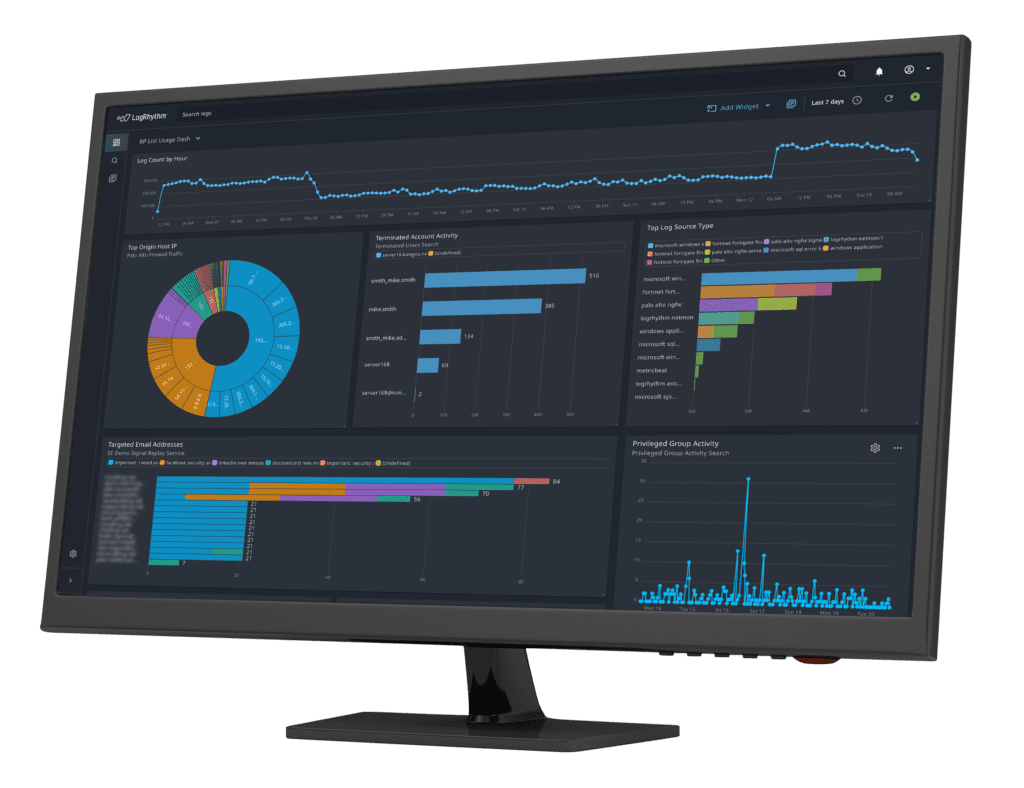
An intuitive interface and frequent delivery of enhancements provide advanced security monitoring capabilities without the administrative burden of a traditional SIEM.
Data ingestion, normalization, and enrichment across all of your SaaS, self-hosted cloud, and on-premises infrastructure enables rapid detection, rich analytics, and powerful searchability.
Investigative workflows are driven by analytics rules mapped to proven frameworks like MITRE ATT&CK®, to help improve security team efficiency and reduce time to respond.
LogRhythm Axon has out-of-the-box integrations with an extensive collection of SaaS applications and cloud infrastructure platforms. API and webhook-based integrations, along with cloud-based data collectors, make it easy to enable new platforms with reliable, high-performance data ingestion.


Using LogRhythm Axon to optimize your cloud security monitoring helps your organization unlock the business benefits of the cloud without compromising on your security or compliance posture. Talk to one of our experts to learn more about how LogRhythm can help your team transform your cloud security monitoring approach.

