Endpoint Monitoring & Investigation
Detect endpoint anomalies — eliminate compromised hosts
In just one click, a threat actor could compromise an endpoint through a spear phishing attack. Your internal servers are vulnerable to threats operating from within.
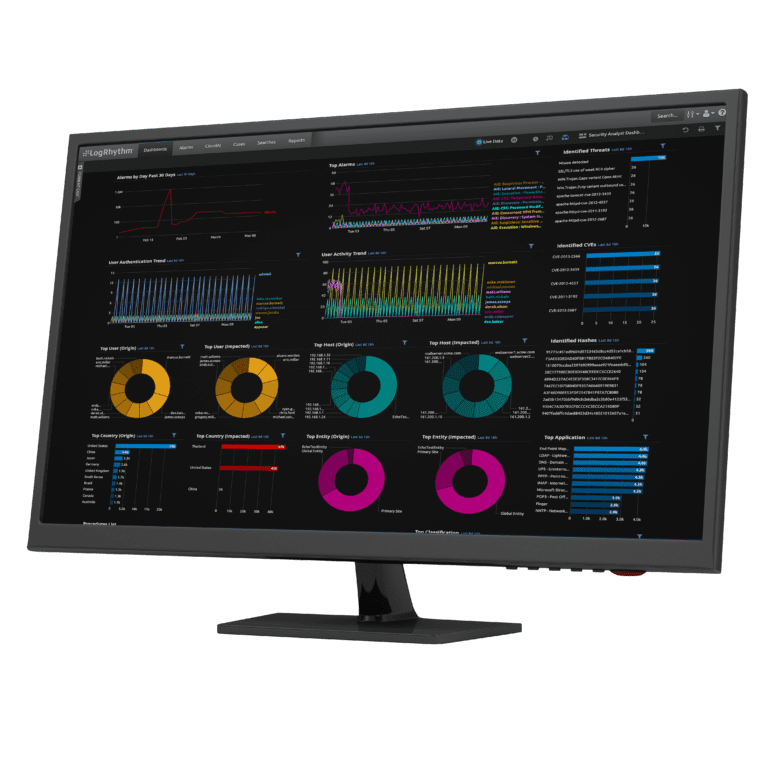
Traditional endpoint protection is no longer up to task. You need a second line of defense. Combining real-time endpoint monitoring with big-data analytics can detect advanced attacks and insider threats. This visibility also provides incident responders access to rich forensic data that can expedite investigations. Get the visibility you need with System Monitor.
When you suspect an intrusion, you need to be able to qualify the threat and assess its potential impact. But you can’t respond to what you can’t see.
Capture a wide variety of the activity occurring on your endpoints and servers in real-time. Search rich forensic data in just seconds to understand when and how the incident occurred, and then contain the compromise with Endpoint Lockdown™.
Protect your enterprise from the unknown. Detect advanced attacks on endpoints and servers. Enable fastest incident response. System Monitor gives you deep visibility into the threats faced by your endpoints. It has a lightweight footprint, support for multiple platforms and policy-based administration. Get the clarity you need for peace of mind for a low cost of ownership.
You can think of System Monitor as a DVR. It continuously records activity occurring on the monitored host in real-time. This data is transmitted and safeguarded for analytics and incident response support.
Unexpected changes to files or the windows registry can indicate the presence of a threat. Detect them and identify change management processes gone awry. Learn more about File Integrity Monitoring.
System Monitor records local process activity, network communication and user activities. This data is used to detect the presence of advanced malware and other threats.
Rest assured knowing that you’re recording when all data transferred to a USB drive and other writeable media. If data leaves your building by foot, you’ll know. With System Monitor, you can also prevent data loss by disabling writable media.
Our platform works with a wide variety of Windows, Linux and Unix operating systems. We also support point-of-sale systems to help customers detect retail cybercrime. Learn more about cyber crime and fraud.
Keep administrative costs low with policy-based configuration and centralized administration. Agent upgrades occur in seconds with the click of a button.
We built our platform for scale. With our enterprise-grade administration, you can deploy and manage tens or hundreds of thousands of agents cost effectively.
The volume of data generated by endpoint monitoring solutions can be significant. Easily deploy System Monitors to sit silently on hosts. When you need to see more, centrally turn up the volume in seconds.
Interested in learning more about protecting your endpoints? Request more information to see how LogRhythm can help.