LogRhythm’s built-in Case Management provides end-to-end threat lifecycle management, but in order to maximize efficiency and provide key performance indicators (KPIs), a case tagging schema needs to be chosen and implemented. Without a standardized schema, WebUI users may make up their own tagging schema, or not use tagging at all—both of which can lead to a lack of visibility.
You can use various case tags to increase network visibility and attain actionable information. For example:
- Make use of a tagging attack type to accurately report on the most common attacks the enterprise faces.
- Include a SmartResponse tag to show which SmartResponses are most frequently used.
- Employ a threat source tag to understand if your threat intelligence sources are generating successful matches or false positives.
Without a tagging schema, such as that listed above, many business security insights can be a challenge to obtain visibility into.
Case tag taxonomy isn’t something new, it is simply collating security best practices with business output requirements from the security business unit.
LogRhythm Case Tags Schema
LogRhythm Case Management comes with a powerful tagging system, but how do you design and standardize a schema to best make use of cases?
The following example will help get you to implement strong case taxonomy and obtain demonstrable business value.
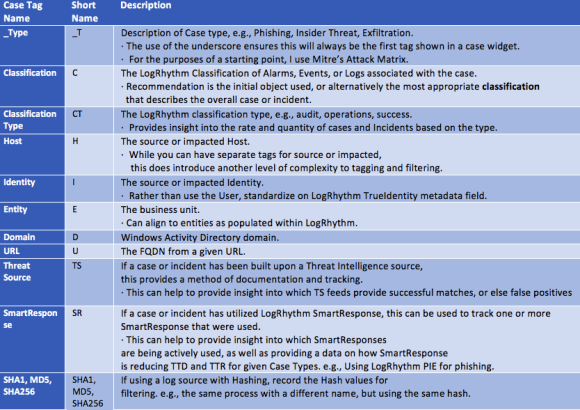 Figure 1: Example LogRhythm Case Tag Schema (Click Image to Enlarge)
Figure 1: Example LogRhythm Case Tag Schema (Click Image to Enlarge)
Using Case Tags in WebUI
The following are several examples of demonstrating the use of a Case Management tag schema within the LogRhythm WebUI:
Filtering
Case tags can be used for filtering closed or open cases. Below, you can see an example of applying a filter for all audit cases using the Tag _ct:Audit. Multiple tag filters can be applied. You can filter this example further to zero in on cases pertaining to a given business entity, host, or even user. This filtering only works if you have been appropriately tagging cases.
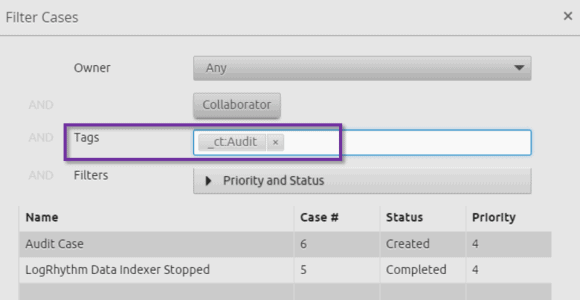 Figure 2: Applying a Filter for All Audit Cases Using the Tag _ct:Audit (Click Image to Enlarge)
Figure 2: Applying a Filter for All Audit Cases Using the Tag _ct:Audit (Click Image to Enlarge)
Case Dashboard
WebUI includes case dashboards, which you can incorporate into and make use of in your tagging. For example, your dashboard can include classifications such as the following:
- Classification Type: Audit, Security, Operations
- Attack Type: Mitre Attack Matrix
- Business Entity
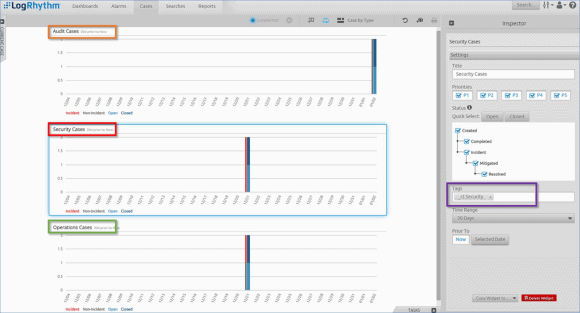 Figure 3: Example of a Case Dashboard Showing Cases by Classification Type, such as Audit, Security, or Operations (Click Image to Enlarge)
Figure 3: Example of a Case Dashboard Showing Cases by Classification Type, such as Audit, Security, or Operations (Click Image to Enlarge)
Tag Reporting
Tags can also be reported within the LogRhythm Reporting Engine and exported either as PDF or to CSV for external data analysis.
Audit History
All activity within a case is audited, including tags. The extended case tagging schema enables you to discover detailed activity, such as when one case was added or removed from another case.
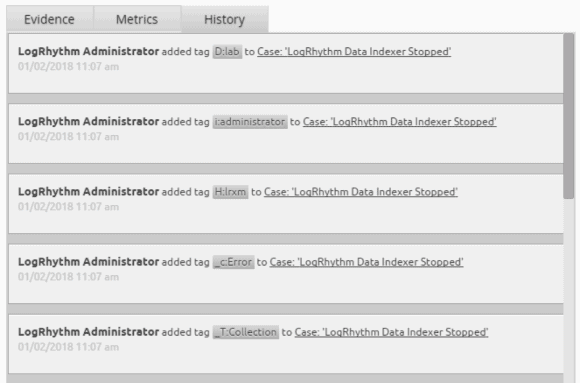 Figure 4: Case Tags Activity Being Audited When Added or Removed from a Case (Click Image to Enlarge)
Figure 4: Case Tags Activity Being Audited When Added or Removed from a Case (Click Image to Enlarge)
Making the Most of WebUI Space
Abbreviating case tags is a great to make the most of the WebUI’s screen real estate. Rather than using full key name, such as Type, Domain, Entity, the below example just uses the first letter of each word.
Another best practice is prepending the most important fields with an underscore. Case tags are sorted in alphabetical order, so an underscore at the beginning of a tag will allow it to appear first in the list—such as the case with the below Type (_T). Finally, if you do need to see more details than are visible on the case panel, you can easily click into the case itself and see full tag data.
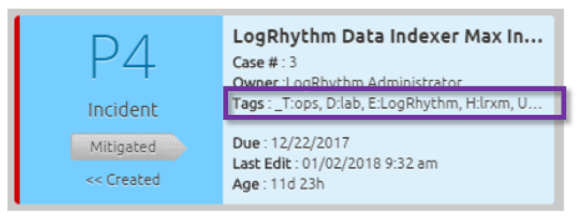 Figure 5: Using Abbreviated Case Tag Schema to Make the Most of the Available Screen Real Estate (Click Image to Enlarge)
Figure 5: Using Abbreviated Case Tag Schema to Make the Most of the Available Screen Real Estate (Click Image to Enlarge)
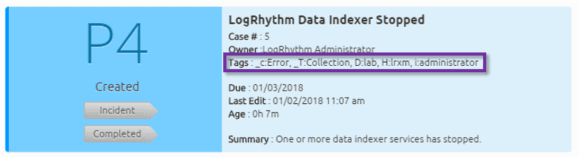 Figure 6: Clicking into the Case to See the Full Details of All Tags Assigned to a Case (Click Image to Enlarge)
Figure 6: Clicking into the Case to See the Full Details of All Tags Assigned to a Case (Click Image to Enlarge)
Optimizing Case Management with Case Tags
LogRhythm’s case tags provide a powerful workflow and ensure accuracy of case management. They also provide KPIs of the services being delivered by the LogRhythm NextGen SIEM Platform. To start utilizing case tags and obtaining demonstrable business value, you simply need to implement a tag taxonomy.