Remote access has become crucial for business operations, as satellite employees and travelers need remote access to corporate networks. However, while remote access greatly benefits productivity, it also exposes the organization to a number of additional threats.
Let’s look into how you can identify and respond to these threats, so you can plug any security gaps that may exist within your organization.
Threat Detection Through User and Entity Behavior Analytics (UEBA)
LogRhythm’s User Threat Detection module (UTD) includes several pre-built AI Engine correlation rules that detect remote access account anomalies. LogRhythm’s built-in Machine Data Intelligence enables these UTD correlation rules to run against a variety of devices, looking for specific events relating to remote access. Added contextual intelligence provides the full context needed for advanced correlation.
One of the metadata fields pertinent to detecting remote access account anomalies is Geographical Intelligence. By utilizing a database of IP address linked to geographic locations, the LogRhythm NextGen SIEM Platform can track user activities all the way down to the city level. This metadata field not only helps to drive AI Engine use cases, but the field also helps speed up forensic investigation by automatically providing context on the source or destination location.
Security Intelligence in Action: Detecting Concurrent VPN Connections
Let’s look at an example of this use case in action.
ACME Labs has several offices around the United States. While a small portion of their staff travel, the vast majority are not expected to remotely connect to the corporate network from outside of their home state and definitely not outside their home country. In this use case, a user account that is not expected to travel suddenly connects to the corporate network from a remote location.
LogRhythm’s AI Engine quickly detects the concurrent VPN logins and queues up an escalated SmartResponse™ alert.
Click on images to view larger
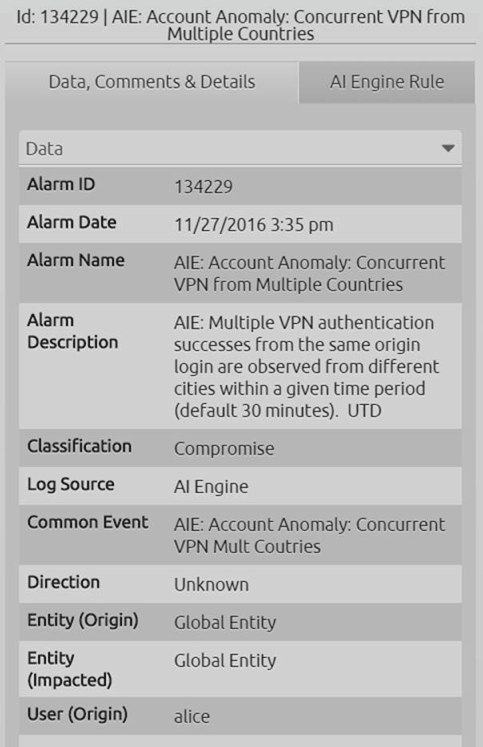
Figure 1: High-Priority, AI Engine Alarm Indicating Abnormal User Behavior
Inspection of the alarm details reveals the user account involved in this incident.
Figure 2: Alarm Details Revealing User Information
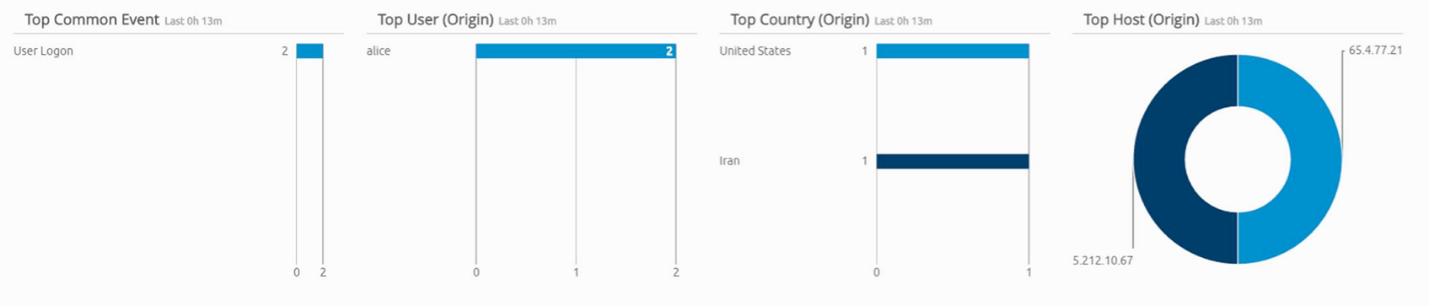
Further drill down into the underlying raw logs associated with this alarm shows the source IP addresses that initiated the VPN connections, as well as the derived metadata showing the geographic login locations and the associated user.
Figure 3: User Remote Access Data
As previously mentioned, the user in question rarely operates outside the United States. So, a keen investigator must ask, should the account be connecting from another country?
Most likely no. Let’s dig a deeper.
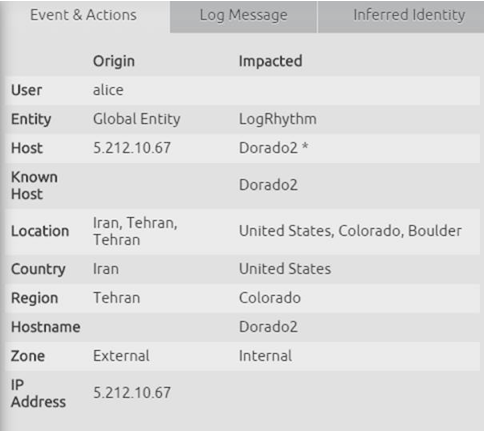
Specific details on each individual log message that triggered this AI Engine correlation rule can be seen with just a single click.
Figure 4: Alarm Drill Down Revealing Typical Behavior
Figure 5: Alarm Drill Down Revealing the City Remote Access was Achieved
At this point, an analyst has the ability to take the next step in the response workflow to ascertain whether this is legitimate behavior. Is this user on holiday? Is he or she traveling? Have his or her credentials been compromised?
All of these questions can be answered utilizing LogRhythm’s built-in security orchestration, automation, and response (SOAR) workflow capabilities. From the Case Management tab, requests for information can be escalated to the appropriate channel, (e.g. the user, a manager, Human Resources, etc.) to validate status. Download our data sheet to learn more about our SOAR security solution, RespondX.
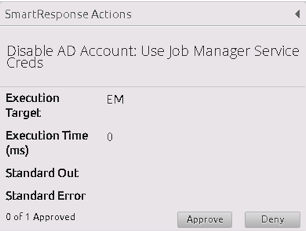
An analyst can also continue to investigate to better understand the user’s activities. If the activities continue to indicate suspicious account behavior, immediate action via SmartResponse can be taken to disable the user account at Active Directory.
Figure 6: SmartResponse to Disable Suspicious Account
Plugging the Gaps Left Open by Remote Access Anomalies
This is a simple, yet effective, use case to help mitigate cyber risks. VPN and remote access is as common attack vector and a typical problem seen by most SOCs today. Take the time to understand the different remote access use cases and plug the gaps within your organization.
This use case is just one of the many variations that are included with the LogRhythm Security Intelligence and Analytics Platform to detect and respond to remote access account anomalies. Other variations on this use case included within LogRhythm, or that can be built upon from built-in AI Engine rules, include:
- Remote connection from unusual VPN source location
- Remote connection from blacklisted VPN source location
- Remote connection from privileged users
- Remote connection from disabled or terminated staff
- Remote connection from contractors or third parties
- Remote connection from staff on annual leave
- Remote connection from C-level staff
To learn more about detecting and responding to remote access anomalies, schedule a demo with a LogRhythm expert.