Reduce Risk with SIEM Solutions
Security teams are often overwhelmed with managing massive amounts of log data from disparate systems. Security information and event management (SIEM) solutions help SOC teams centrally collect data across the environment to gain real-time visibility and better detect, analyze, and respond to cyberthreats.
Using SIEM technology can improve the effectiveness of your security team and help you more quickly pinpoint accurate cyberthreats before they become damaging breaches, reduce the impact of security incidents, and comply with mandates.
Get an Inside Look at a
SIEM Solution
Want to see how a SIEM solution works? In this product tour, we’ll guide you through SIEM features and capabilities that help security professionals more easily detect cyberthreats.
Benefits of Leveraging SIEM as Your Security/IT Foundation
SIEM solutions map to modern operational needs, delivering real-time visibility, efficient and secure data access, streamlined workflows, a unified user experience, and the ability to customize how you manage your environment.
Value for security and IT operations
- Effective collection and normalization of data to enable accurate and reliable analysis
- Real-time visibility across your environment to quickly identify and prioritize potential issues
- Ease of accessing and searching across raw and parsed data for investigation and compliance
- Ability to map your security and IT operations to existing frameworks such as NIST and MITRE ATT&CK
Broad integration across security and IT vendors
- Support for integration with hundreds of security and IT solutions to further extend SIEM capabilities and data collection
- Central management of all security related solutions that ties together disparate solutions to provide a single pane of glass
Compliance adherence and reporting
- Ensure compliance adherence with real-time visibility and notifications to ensure awareness of all compliance-related activity
- Prebuilt compliance modules automatically detect violations as they occur to remove the burden of manually reviewing audit logs
The Evolution of SIEM Software
As SIEM software has transformed over time, the core components continue to provide value, while new, innovative technology — such as automation and new analytical techniques — has been built on top of the traditional SIEM foundation to provide the most comprehensive approach to reducing risk across an organization.
This evolution of capabilities and features is often referred to as “next-gen SIEM.” The deployment of a next-gen SIEM solution delivers enhanced methods for securing data and solidifying operational excellence.
There are three key elements that make up the foundation of all leading SIEM solutions:
- Data quality: Effectively ingest and normalize data to enable more precise search and analysis
- Scalability: Scale in parallel to an organization’s growth to collect, normalize, and analyze an increasing quantity of data
- Flexible deployment options:
- SaaS
- Cloud deployment
- On-premise
The integration of threat intelligence with foundational SIEM capabilities provides additional threat context that can help deliver faster mean time to detect (MTTD) and can ease some of the burden of incident investigation.
Threat intelligence feeds typically include malicious:
- IPs
- URLs
- Domain names
- Email addresses
- Filenames
- Hashes
- Registry keys
- DLLs
Behavioral analysis provides a unique look at the activity of users and network entities to be able to prioritize and address behavior that shows significant deviation from normal behavior. UEBA solutions use machine learning (ML) to determine both the baseline (normal behavior) of each user and entity and the significance of any activity that deviates from that baseline.
UEBA use cases
- Data exfiltration
- Service account misuse
- Insider access abuse
Analysis of network traffic and packet data delivers visibility into the communication methods and patterns between networked devices. NTA solutions can be leveraged as a set of rules, looking for specific patterns and behavioral outliers, or as an effective means for performing threat hunting.
NTA use cases
- Application usage
- Data exfiltration
- Bandwidth utilization
Endpoint monitoring enables operations to track activity on an endpoint that includes the viewing, creation, modification, and deletion of files. This ability to track file access and modification is often delivered through an endpoint solution that includes file integrity monitoring (FIM) as part of the feature set.
Endpoint Monitoring use cases
- Forensic analysis
- Data exfiltration
- Sensitive data access
SOAR is an underlying set of capabilities that increase operational efficiency and collaboration across all the other layers of a next-gen SIEM platform. These capabilities include case management and contextualization for incident investigation, and playbooks for streamlining operational workflows.
LogRhythm's SIEM Solutions | Self-Hosted & Cloud-Native Options
Depending on your business use cases, LogRhythm has flexible deployment options with our SIEM solutions to protect your on-prem, hybrid, or cloud environments.
LogRhythm SIEM (self-hosted)

LogRhythm SIEM is a self-hosted SIEM platform that provides holistic visibility into your network, out-of-the-box content, and compliance automation modules.
LogRhythm Axon (cloud-native)
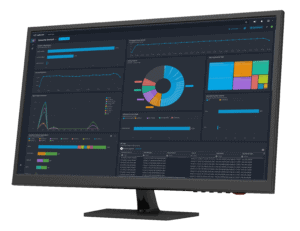
LogRhythm Axon is a cloud-native SIEM solution. It’s built to easily scale and manage and reduces the burden of managing operating infrastructure.
Want to Talk More About SIEM Solutions?
With over 20 years of cybersecurity experience in the SIEM space, we’re here to answer any questions you may have about reducing risk to your organization.
