What is SIEM?
SIEM stands for security, information, and event management. SIEM tools aggregate log data, security alerts, and events into a centralized platform to provide real-time analysis for security monitoring.
Security operation centers (SOCs) invest in SIEM software to streamline visibility of log data across the organization’s environments, automate security workflows, detect and respond to cyberthreats, and adhere to compliance mandates.
Before we dive deeper into all things SIEM, here are the following topics you can click to.
- How Does SIEM Work?
- Benefits of SIEM Technology
- The Evolution of SIEM Software
- Deploying SIEM Technology
- Investing in a SIEM Solution
- SIEM Examples
How Does SIEM Work?
Cybersecurity is a challenging job, and many organizations lack the personnel or resources to properly manage the threat landscape effectively. SIEM tools help alleviate common security team challenges regarding log management, threat management, workload capacity, compliance, and more. Let’s dive deeper into how SIEM software works.
Log Management
SIEM software starts with managing and consolidating log data for holistic visibility across the environment.
- Log Collection and Aggregation: SIEM software collects log and event data produced from applications, devices, networks, infrastructure, and systems to draw analysis and provide a holistic view of an organization’s information technology (IT). The log data is aggregated from various sources and normalized to a common format for easier analysis. These sources can generate logs in different formats such as syslog, JSON, and XML.
- Log Parsing and Enrichment: Raw logs are difficult to search and understand, which makes threat hunting challenging for security analysts. SIEM tools parse and enrich raw entries with contextual information to make it readable for humans to analyze. For example, SIEMs break down data into digestible information such as timestamps, event types, source IP addresses, usernames, geolocation data, user context, and more.
- Log Storage and Retention: SIEM tools store log data in a centralized repository for extended periods which helps with forensic investigations, historical analysis, and compliance requirements.
Event Correlation and Security Analytics
Analyzing log data in real-time, a SIEM uses rules and statistical correlations to drive actionable insight during forensic investigations. SIEM technology examines all data, sorting the threat activity, and assigning it with a risk level to help security teams identify malicious actors and mitigate cyberattacks quickly. SIEMs can leverage real-time analytics, batch analytics, data science algorithms, and user- and entity-based analytics to draw analysis.
Threat Detection, Investigation, and Response
When managing incidents and responding to threats, SIEM tools help streamline this process with:
SOAR: SIEM tools often integrate SOAR into the security workflow to automatically respond to cyberthreats and shut down attacks in real time. SOAR capabilities help SOC teams reduce redundant tasks and improve meant time to respond (MTTR) to cyberthreats.
Case Management: When investigating or responding to a cyberthreat, SOCs can use case management as a central repository to annotate and track forensic evidence, as well as collaborate between team members. Cases can be shared with others or restricted based on confidentiality. Using case management, SOC teams can provide a real-time status report of an ongoing investigation or an audit trail of all related activity. Case management enables organizations to drastically improve incident response efficiency.
Playbooks: Security analysts use playbooks to streamline detection and response. Playbooks are predefined guides or documentation that provide step-by-step instructions for responding to certain threats or attacks. For example, organizations can leverage playbooks for threat hunting, ransomware, and malware backdoors. Like LogRhythm, SIEM vendors can provide playbooks out-of-the-box, but every organization is also encouraged to customize playbooks based on their unique needs.
If you’re interested in seeing examples of these features, watch this SIEM demo for an inside look at how a SOC analyst quickly responds to a phishing attack using SOAR, case management, and playbook capabilities.
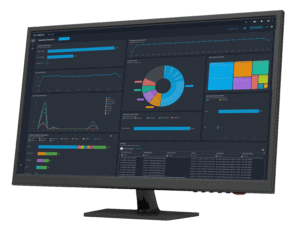
Dashboards and Reporting
SIEMs use dashboards built with graphics and customized widgets which help security analysts interpret and understand security information. Dashboards are an essential part of SIEM tools that display real-time status of all threat activity so that analysts can easily interpret context and drill down for further investigations.
Security teams can easily pull and download reports from the SIEM platform. Integrations with other software like Kibana can also provide advanced insights for measuring and reporting on SOC metrics.
Compliance Management, Auditing, and Reporting
An important use case for why organizations invest in SIEM technology is because they must abide by government compliance mandates — especially those operating in highly regulated industries. SIEM software helps organizations with continuous monitoring requirements, analyze potential control violations, store long-term records, and provide reports to analysts, management, or auditors.
SIEM vendors can reduce the burden of assuring regulatory compliance by deploying prebuilt reports for audit and management review and detecting compliance violations automatically. For example, LogRhythm’s Consolidated Compliance Framework provides prebuilt compliance automation modules for an array of regulations and frameworks, including:
- CIS Critical Security Controls
- CMMC
- GDPR
- HIPAA
- NIST (800-53, 800-171, CSF)
- PCI DSS
- And much more!
Learn how LogRhythm streamlines compliance with SIEM ->
Benefits of SIEM Technology
Depending on the solution and vendor, SIEM components can provide a wide variety of benefits that help to increase overall security posture, including:
- Centralize Security Management and Reduce Visibility Gaps: By consolidating log data from disparate systems, SIEM tools provide a centralized workflow that allows for real-time visibility across the environment. It helps reduce visibility gaps to ensure cyberthreats are not missed. SIEM provides an easier way to collect and manage large sets of data, all in one place.
- Reduce Manual Tasks with Automation: Security professionals can reduce manual workload by using automation for mundane tasks so that analysts can focus on more strategic work.
- Detect a Wide Variety of Threats: Humans simply can’t do this job alone. SIEMs help organizations reduce risk to a variety of attacks ranging from ransomware, phishing, insider threats, advanced persistent threats (APTS), and more. SIEM vendors can also provide the ability to map operations with common attack tactics by aligning to frameworks such as MITRE ATT&CK®.
- Improve Detection and Response: SOC teams can reduce metrics such as mean time to detect (MTTD) and MTTR. Alarm prioritization helps security teams easily respond to high-risk threats and prioritize incident response.
- Ease Compliance Auditing and Reporting: Businesses operating in highly regulated industries can ensure compliance adherence and reduce the chances of costly fines.
- Improve Analyst Experience: If configured and maintained properly, SIEM tools help security analysts tell a better story with the data, detect a variety of attacks, and streamline their operational workflow. SIEMs provide real-time visualizations and context into cyberthreats, turning disconnected log data into meaningful insights.
The Evolution of SIEM Software
SIEM tools have been around for over 15 years, but today’s modern SIEMs have evolved from their original counterparts. Mark Nicolett and Amrit Williams established the term “SIEM” in a 2005 Gartner research report, Improve IT Security With Vulnerability Management. [1] These legacy SIEMs were a combination of integrated security methods into one management solution, including:
- Log management systems (LMS): Processes for simple collection and centralized storage of logs.
- Security information management (SIM): Tools for automated collection of log files for long-term storage, analysis, and reporting on log data.
- Security event management (SEM): Technology for real-time monitoring and correlating of systems and events with notification and console views.
As SIEM software transformed over time, the core components continue to provide value, but innovative technology within the competitive landscape paved the way for more comprehensive and advanced approaches to reducing risk in an organization. This led SIEM providers to eventually launch new features that have termed these enhanced products as “next-generation SIEM” solutions.
Next-Gen SIEM vs. SIEM
What are the major differences between traditional SIEM tools and next-gen SIEMs? At the core, both solutions have similar functionality, but legacy SIEMs can’t handle the rising volume and complexity of data in today’s threat landscape. With the increase in cloud adoption, mobile technologies, hybrid datacenters, and remote workforces, next-gen SIEMs are much more suited to meet the growing demand for threat detection and response across disparate systems.
Next-gen SIEMs provide new capabilities for improving security visibility and threat detection, while also streamlining the process for security teams to manage their workload. Some core components of a next-gen SIEM software, include:
- Open and scalable architecture: Ability to streamline data from disparate systems across on-prem, cloud, and mobile technology, in a single entity.
- Real-time visualization tools: Features that help security teams visualize related security events to depict threat incidents accurately.
- Big data architecture: Ability to collect and manage large, complex data sets for indexing and structured and unstructured search.
- UEBA: Solution for monitoring behavioral changes in user data to detect anomalous instances when there are deviations from “normal” patterns.
- SOAR: Technology that automates routine, manual analyst actions to increase operational efficiency throughout the incident response workflow.
Lastly, with the increase in cloud adoption, mobile technologies, hybrid data centers, and remote workforces, today’s modern SIEMs are much more suited to secure data and SaaS applications in the cloud. In the next section, we’ll dive deeper into SIEM deployment approaches.
Deploying SIEM Technology: Cloud, On-Prem, & Hybrid
SIEM tools can be deployed as a cloud-based service or support an on-prem deployment. This strategy largely depends on business and security requirements.
On-Prem SIEM Deployments
Here are reasons why organizations choose to deploy on-prem SIEM solutions today.
- Data Control: Compliance requirements are a common business use case for opting in for an on-prem (or self-hosted) SIEM deployment. We see it with LogRhythm customers all the time. For some organizations, having complete control and ownership over their data and infrastructure is necessary to operate in regulated industries such as healthcare or finance.
- Legacy Systems: Many organizations have legacy systems that are difficult to integrate with cloud services and therefore maintain self-hosted deployments to avoid disruption.
- Cost Control: Some organizations prefer this model because they have more control over ongoing operational costs dealing with hardware maintenance or upgrades.
Discover LogRhythm’s self-hosted SIEM solution ->
Cloud-Based SIEM Deployments
In today’s digital world, many business models require SOCs to secure SaaS applications in the cloud. That is one example of why many organizations have shifted from a client-hosted model to a cloud-native or cloud-delivered deployment model. Cloud SIEM is the most prominent deployment architecture today for many reasons, such as:
- Rapid Deployment: Cloud SIEM solutions can be set up more quickly than on-premises alternatives, allowing organizations to start monitoring and protecting their environment sooner.
- Scalability: Cloud-based SIEM solutions can scale more easily to accommodate growing data volumes, workloads, and users.
- Ease of Management: Cloud SIEM customers do not need to manage the operating infrastructure and can focus more on detecting and responding to threats, while the Cloud SIEM provider handles hardware provisioning, software updates, and security patching.
- Flexibility: Cloud SIEM solutions can be accessed from anywhere with an internet connection, making them suitable for organizations with distributed teams or remote workforces.
- Cost Efficiency: While cloud SIEM solutions involve recurring subscription costs, they can be cost-effective for organizations that prefer an OpEx (operational expenditure) model over a CapEx (capital expenditure) model.
- Disaster Recovery: Cloud SIEM solutions may come with built-in disaster recovery and backup capabilities to help organizations quickly recover from data loss or system failures.
Discover LogRhythm’s Cloud-Native SIEM solution ->
Hybrid SIEM Deployment
Some organizations use a hybrid approach, where they deploy a SIEM on-prem for certain sensitive data or legacy systems, while using a cloud-based SIEM for other parts of their infrastructure.
The choice between on-prem and cloud SIEM deployment should be driven by an organization’s unique needs, security considerations, budget constraints, and future growth plans.
Investing in a SIEM Solution
Before investing in a SIEM tool, gather your business requirements and evaluate your security objectives and priorities. It can be an investment up front, but SIEM software helps security teams achieve compliance and mitigate risks quickly — saving the business from significant financial implications or legality issues if a breach were to occur.
When choosing a SIEM, understand how licensing models determine the true total cost of ownership (TCO) and take into account future growth as your organization may expand over the years. It’s critical to find a trusted provider that aligns to the needs of your business for long-term scalability, while also helping your team effectively deploy a solution quickly to get the highest return on investment.
Once you deploy a SIEM, there is still a lot of work to do. This is not a tool where you can set it and forget it. You should constantly refine processes and mature security workflows. Although SIEM tools can greatly improve the SOC analyst experience, they require proper configurations, tuning, and testing. Many security vendors provide out-of-the-box content or embedded expertise to provide immediate value, but prioritizing your custom use cases is just as important.
Upfront, ensure your security partner provides quality training or SOC services to help assess and mature your security maturity along the way. If needed, some organizations seek help from managed service security providers (MSSPs) due to a lack of resources.
Examples of How to Use a SIEM Tool
 Interested in learning more about SIEM and how SIEM works? Check out this SIEM product tour that shows you a behind the scenes look at our cloud-native SIEM platform, LogRhythm Axon.
Interested in learning more about SIEM and how SIEM works? Check out this SIEM product tour that shows you a behind the scenes look at our cloud-native SIEM platform, LogRhythm Axon.
It guides you through video tours of how security analysts can use SIEM capabilities and dashboards to more easily detect and respond to cyberthreats. Explore the video chapters at your own pace!
