LogRhythm’s Analytic Co-Pilot Services helps customers around the globe streamline use case development, tuning, and investigations. To keep up with the latest threats and trends within the industry, we work with our customers to build comprehensive coverage and leverage security information and event management system (SIEM) best practices.
In this blog, we’ll dive into some of the interesting use cases developed in the first quarter of 2023. Although customers have unique and interesting challenges, which can be industry or company specific, many use cases can be transferrable with little or no customizations. Sharing this knowledge may help you reduce the time and effort to create certain rules from scratch and you can also learn how to tune such uses cases.
From our latest quarter, we have seven new security use cases to share. To understand the complexity of a use case and how it may apply to your environment, we provide a key at the start of each one to explain:
- Where the use case originated from, either a custom rule from our team or based upon a Knowledge Base Threat module.
- The log sources required to successfully implement a use case.
- Difficulty score to set up the use case and how complex it may be.
- Impact rating to assess how a use case can positively impact threat monitoring.
7 Security Use Cases Based on Customer Needs
1. Detecting Lateral Tool Transfer Using PSExec on Remote System
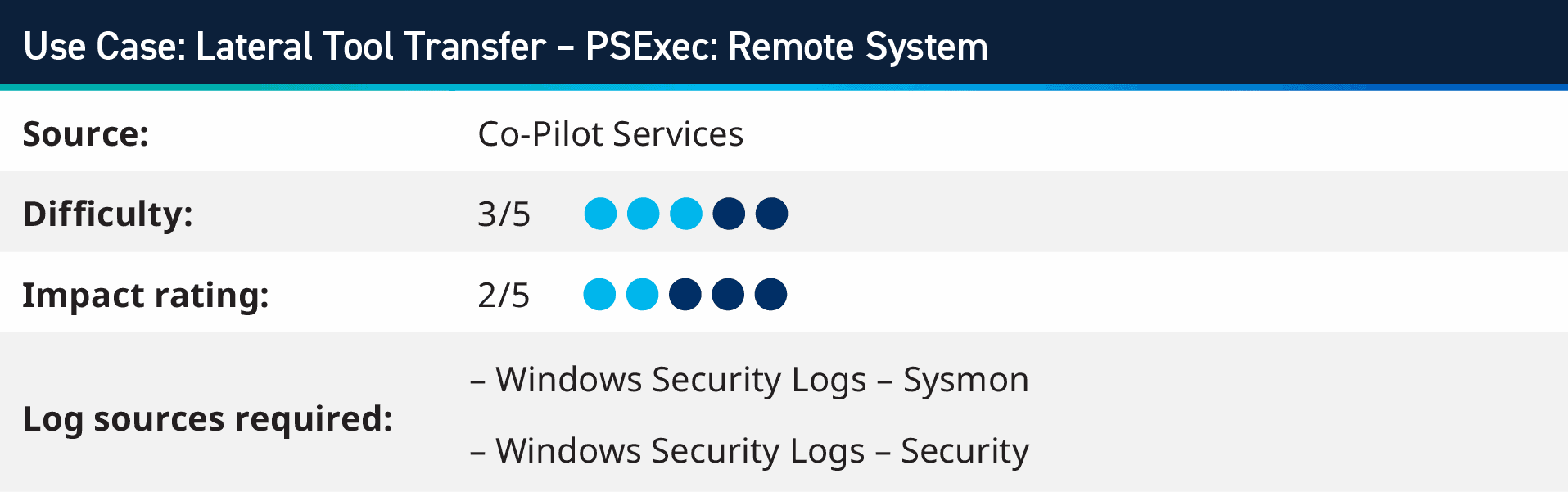
PSExec is a widely used tool that allows system administrators to execute commands on remote systems; however, it’s not just system administrators using this tool, attackers also use PSExec to move laterally and deploy malicious payloads on compromised systems.
Monitoring for the use of PSExec within your environment allows you to identify where it is being launched from and who is launching it. You can whitelist known and expected behaviors from your system administrators, while looking for nefarious uses of the powerful tool.
The way to detect this threat should be approached in two ways; the first is to use Windows Command Line Logging/PowerShell Logging to look for the name of the tool with the parameters that are used to connect to remote systems; however, with the ease of renaming files and executables, it is important to also use Microsoft’s Sysmon output, which includes the hash of the files. By building up a list of hashes, which are known for the different versions of PSExec, you can still track this use cases even if the attacker changes the name of the executable.
When working to tune the false positives of this rule, identifying the legitimate hosts where PSEexec is expected to come from within your environment (e.g. system administrator’s systems or automation systems), as well as which accounts should be executing them is the first step to take.
To learn more about this threat and how it works, watch our video breakdown below!
LogRhythm Co-Pilot customers can download the detection rule and implement it into LogRhythm SIEM by navigating to the Community post here.
2. Detecting a Ransomware Variant Called TuRKey_RanSOmWarE
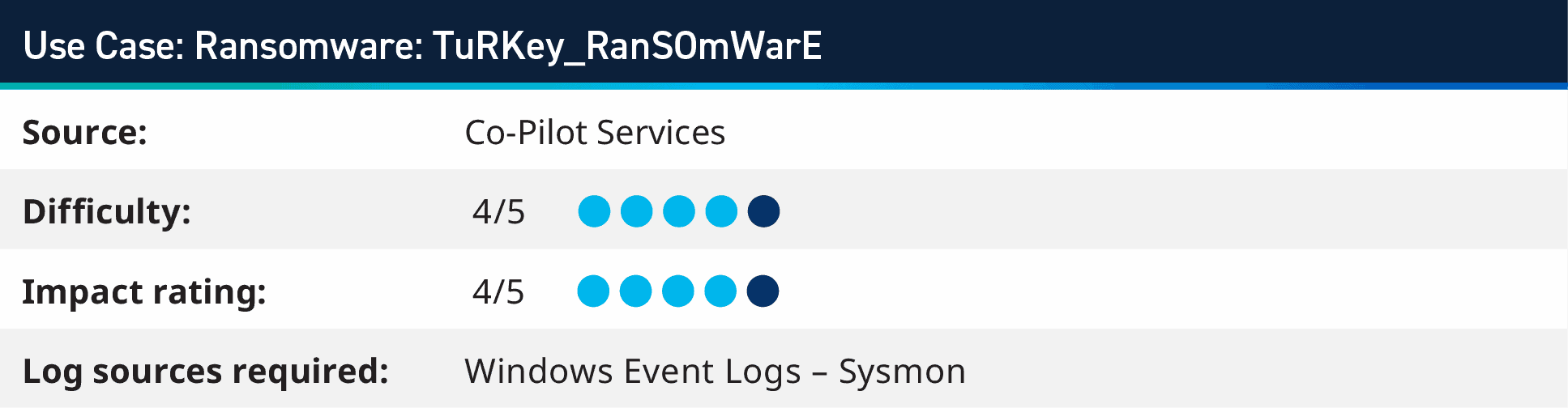
In this use case, we will teach you how to detect a ransomware variant called “TuRKey_RanSOmWarE” that an unknown threat actor has been using. The good news is, that this this type of malware can be identified by various antivirus and endpoint detection and response tools — but there is a catch — if someone tweaks the code and compiles it differently, those same tools might not be able to stop it anymore. That’s why it’s super important for anyone working in security to understand the sequence and pattern of how ransomware behaves.
In this example, after the initial execution of the malware binary XXX.exe, a parent process creates a new process called system.ini.exe. The malware then creates some files, updates the registry, and switches user to SYSTEM.
From the samples we have seen, it looks like the malware is more aimed at trojan-like features rather than typical ransomware strains.
To monitor your environment, there are several indicators of compromise (IOCs) you can focus on; however, LogRhythm’s behavior approach for our AI Engine detection rule is:
- Looking for VssAdmin delete shadows – a typical malware technique to remove restore and backup points in the system
- File creation of five different files from the same process/parent process
- Modification of five different files within the system
You can add in exclusions for executing from within Program Files and known applications, but this rule may require further tuning to ensure the true positives will be prominent.
LogRhythm Co-Pilot customers can download the detection rule and implement it into LogRhythm SIEM by navigating to the Community post here.
3. Detecting OneNote Spawning MSHTA to Prevent QAKBOT Malware
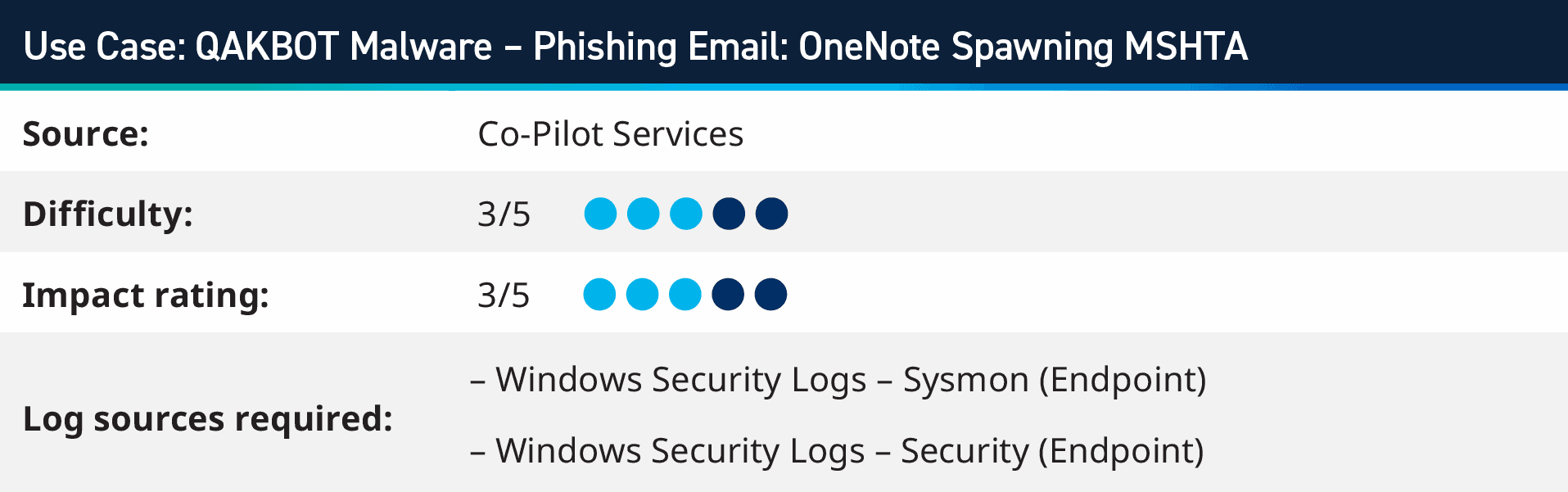
Attackers are becoming creative with delivering payload; one method is spawning MSHTA.exe via a OneNote document downloaded or sent to a victim. Recently, the QAKBOT malware has started incorporating Microsoft OneNote into phishing campaigns. The malware can spread and gain access to sensitive information through seemingly legitimate OneNote files. It is essential for organizations and users to be aware of this new tactic and to take measures to protect themselves against QAKBOT, such as keeping their systems up-to-date with the latest security patches and using robust security solutions.
MSHTA.exe is a native Windows binary designed to execute Microsoft HTML Application (HTA) files, including Script Host Code (VBScript and JScript) embedded in HTML files. A User opening a .one file that has been sent to them will open OneNote which will then utilize the MSHTA.exe to trigger the QAKBOT malware. Security Researcher Florain Roth has also indicated very low AV detection rates for this kind of attack:
There is still a high number of #QakBot dropping #OneNote (.one) phishing email attachments with very low AV detection rates
Detection opportunity:
ONENOTE.EXE spawning mshta.exehttps://t.co/hyTuIC40yd pic.twitter.com/yKxOhEdHs6— Florian Roth (@cyb3rops) February 4, 2023
We can monitor for this by using either the Event ID 4688 from Windows Security logs or Event ID 1 from Sysmon, looking for OneNote.exe spawning MSHTA.exe.

You can expand this rule to monitor for other processes that are triggered from OneNote, as well as other Office Applications. Other avenues for thought around this delivery technique could be considering if your Excel document be launching a Ping or a PowerPoint document running a .bat script? We look at this a little more in Use Case 7 further on in this blog.
LogRhythm Co-Pilot customers can download the detection rule and implement it into LogRhythm SIEM by navigating to the Community post here.
4. Identifying Access Token Manipulation
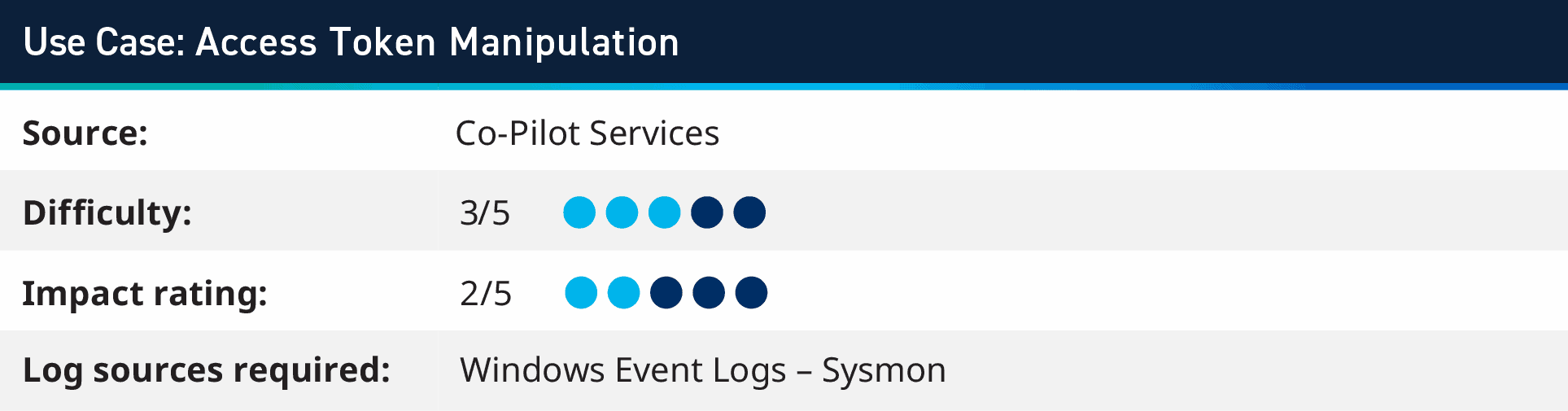
Adversaries can escalate privileges and bypass access controls by duplicating and impersonating another user’s token. This is done by creating a new access token that duplicates an existing token using the DuplicateToken(Ex) function. A PowerShell script and Empire’s GetSystem module are employed to escalate privileges. The script creates a named pipe and launches a service to write to it. When the service connects to the named pipe, the script impersonates its security context. Upon successful execution, the test output reveals the domain and username of the impersonated account, which is the local SYSTEM account.
Monitoring for this attack requires Sysmon logs, looking for three stages; the first, a PowerShell or Batch script being executed; then looking for Named Pipe Created; and finally, the same User and Hostname that created the Named Pipe starting services, performing interprocess communication or object added to Services.
5. Boot or Logon Initialization Scripts – T1037.001
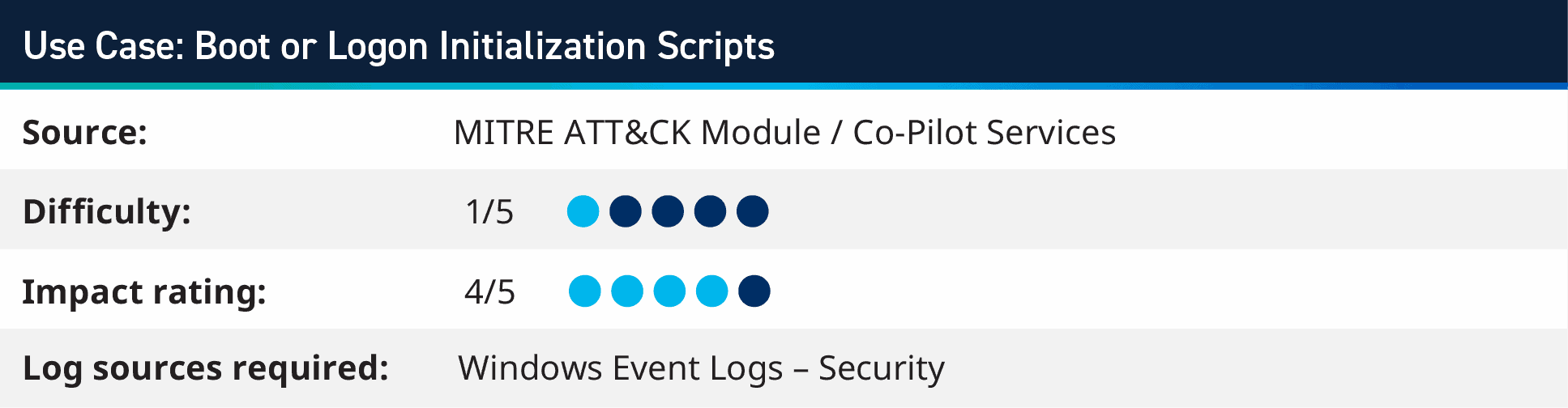
Scripts that will trigger when you either logon to your system or when you first boot your system is a great way for attackers to maintain access to an environment. For example, if a malicious start up script were to launch a reverse shell, open some firewall ports or something else, then if these actions were found and removed by the IT or security team, on the next reboot or login they can regain access to the target system.
This rule is specifically designed to detect when an attacker attempts to create the UserInitMprLogonScript registry key, a well-known persistence and privilege escalation method used by attackers. This rule is crucial in detecting lateral movement and persistence techniques, which are critical steps in an attacker’s kill chain. It is considered a high-level rule as it can signify a severe threat to the organization’s security.
The rule uses the Sysmon log source, monitoring for the command for “reg add” and focussing on the UserInitMprLogonScript path within the registry hive. Although a simple rule, it is effective to monitor for scripts being added for persistent access to a system.
There are a couple of exclusions to add to ensure that things like Group Policy scripts are not causing false positives, but it is straight forward to set those exclude filters.
LogRhythm Co-Pilot customers can download the detection rule and implement it into LogRhythm SIEM by navigating to the Community post here.
6. Top One Million Site List
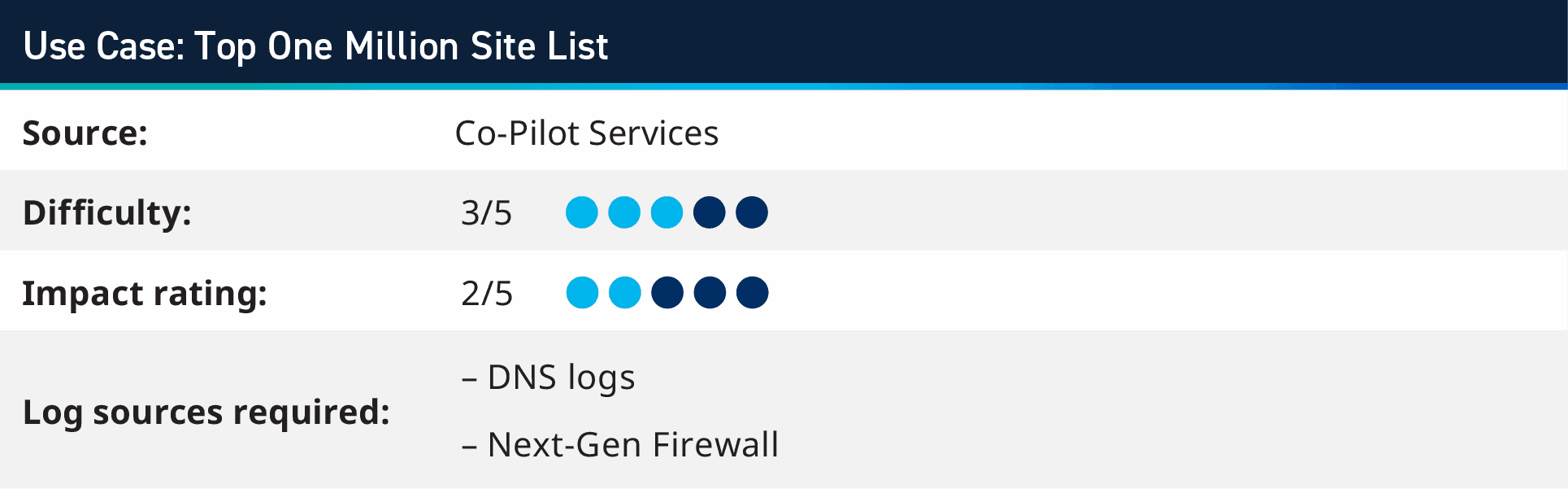
When using lists of IP addresses and domain names within LogRhythm SIEM, it typically references Threat Intelligence feeds, where we have a list of known bad actors and analysts can search for any activity where hosts are connecting to these IOCs. This rule switches the role of a list and populates it with the top one million domains on the Internet from Cisco Umbrella feed within the LogRhythm List Manager. This PowerShell script downloads the compressed file with the list containing the 1,000,000 domain names, extracts it and removes the unneeded data and columns from the file. Once this is done it moves the file, in the right format, to the list import folder on the Job Manager.
This allows you to have an up-to-date list of the top domains accessed on the Internet and you can create a rule which looks for domains that aren’t on that list. There are likely to be some false positives around this, where it may be the domains that you own or services which are specific to you or your industry. Adding a second list of False Positives for other exclusions also allows for ease of tuning, seeing as the script is designed to run regularly and update the One Million Domain List with the latest version – which removes any additions you manually add.
7. Spear Phishing Attachment Document Using Ping – T1566.001
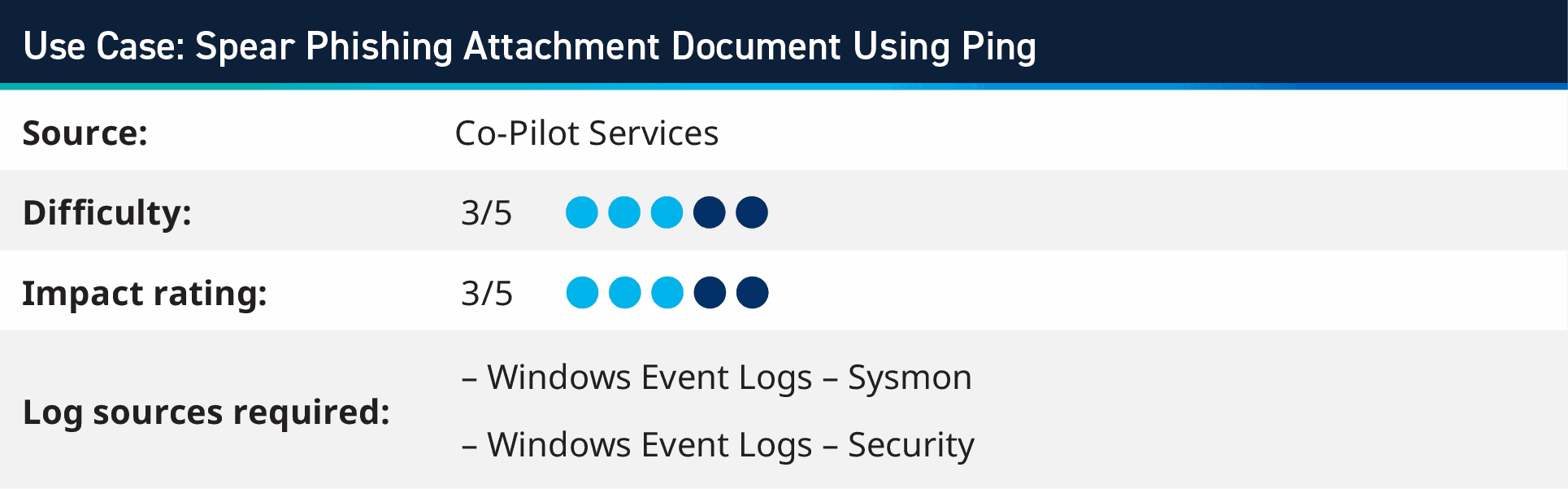
Winword.exe is a legitimate program part of Microsoft Word, while ping.exe is a tool used to test network connectivity; however, if winword.exe runs ping.exe and pings an IP address, it may indicate malicious activity like command-and-control communication. Attackers often use the ping tool to test network connectivity and identify vulnerabilities in a target system. This suspicious behavior could signify a malware infection or an attempt to exfiltrate data.
This use case will require user-workstation logs, particularly Microsoft Security Event ID 4688 with command line information or Microsoft Sysmon logs. These logs provide information on creating new processes on a system, which can be used to identify instances of winword.exe running ping.exe and pinging an IP address.
It is essential to keep logs of user-workstation activity and analyze them for suspicious activity to ensure network security. If this type of visibility is unavailable in the SIEM, our customers may want to configure the EDR solution to monitor and alert them to this specific behavior.
LogRhythm Co-Pilot customers can download the detection rule and implement it into LogRhythm SIEM by navigating to the Community post here.
More Analytic Co-Pilot use cases and resources
During this last quarter, we focused heavily on how we can leverage insights from endpoint logs ingested into LogRhythm SIEM to better analyze different attack vectors, especially around the Office suite launching suspicious processes. Along with endpoint use cases, we worked with customers to look for access token manipulation and boot script initialization.
For our customers with the Analytic Co-Pilot, Support Account Manager, or Technical Account Manager services, these use cases and others are available to download immediately within our Subscription Services Group Hub on the LogRhythm Community! If you’re not a LogRhythm customer, you can still use these use cases as inspiration to apply to your unique threat detection and response needs.
To glimpse over other use cases our Co-Pilot team has worked on in previous quarters, visit the following blogs below:
- Q2 2022 Analytic Co-Pilot security Use Cases
- Q3 2022 Analytic Co-Pilot Security Use Cases
- Q4 2022 Analytic Co-Pilot Security Use Cases
To learn more about our Analytic Co-Pilot Services and how we can improve your threat detection and response, learn more here. If you are a customer and you have questions, reach out to your customer success manager or account team to get more information about how we can help with your use cases and analytics!
