With the ever widening talent gap in cybersecurity and the expanding complexity of the cloud, organizations need an intuitive Security Information and Event Management platform (SIEM) that ensures seamless threat detection, investigation, and response. That is why we built our cloud-native SIEM, LogRhythm Axon, from the ground up. It’s been a year since LogRhythm Axon debuted and over that year, we’ve made significant strides in the product to help make the life of a security analyst easier. With feature releases every two weeks, we’re continually listening to our customers and innovating on the platform; helping increase the efficiency of a security operations center (SOC).
With the latest LogRhythm Axon release, we are streamlining incident response by simplifying case management and investigative workflows. Analysts are getting quicker insight into events that need immediate attention through the automation of case management from analytics rules. And instead of running a separate SIEM to test your environment, we are enabling threat detection engineering from inside the LogRhythm Axon platform. In addition, we are enhancing search functionality, expanding detection capabilities, and giving greater insight into data collection.
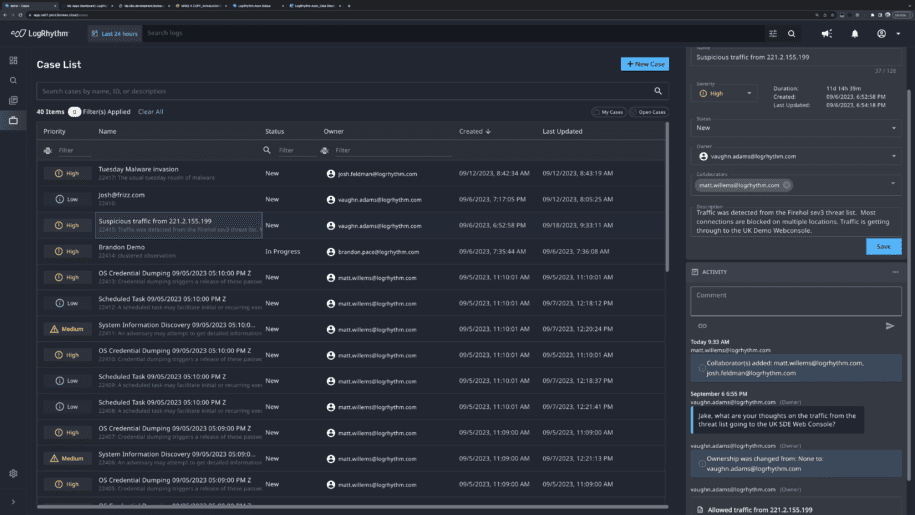
Simplified Incident Response with Case Management
We’ve done a lot of work on developing the LogRhythm Axon architecture to ensure easy access and contextual insight into the data that flows into the platform. By building this to be as automated as possible, we enabled a baseline to do the same with case management. Case management is the home for the analyst workflow within LogRhythm Axon. In place of a manual process that can be both time-consuming and prone to errors, we created case management so alerts can be automatically triggered from analytics rules. When each case is created, any logs that were attached to that observation will be automatically attached to that case, thus enabling quick access for further investigation. All cases are easily tracked, managed, collaborated on, and monitored in real-time in the case management dashboard as well as via email alerts. By having case evidence in one place across team members, you gain faster resolution times, greater efficiency, and better quality information.
Easily Test Your Detections within the LogRhythm Axon User Interface (UI)
The majority of SOCs rely on a secondary SIEM to run test scenarios and to test detections within their environment. With LogRhythm Axon, we’ve simplified this process by enabling the ability to test detections directly within the LogRhythm Axon UI. You can set up and manage playbooks from within the interface and when you add a playbook, you can add replay logs from a file or clipboard and edit in line for each specific log. With this capability, you can easily test your analytics rules to ensure they are fine-tuned and optimized for your environment as well as run red team exercises and penetration tests to check for exploitable vulnerabilities.
Enhanced Search Functionality with Common Events
Searching for logs is one of the primary functionalities of a high-performing SIEM but searching, depending on which SIEM vendor you utilize, can be a difficult task as logs come in all shapes and sizes. At LogRhythm, we utilize a feature called Common Events which helps find relevant security events across different vendors’ log sources without needing prior knowledge of the underlying log structure. With searching by common event, you can easily see the logs that are being represented within that common event, granting you the ability to easily hunt into the activity that happened during an incident. In addition, you can now search by special characters and Regex, making advanced searches more accessible.
Expanded Detection Capabilities
With the introduction of the Count Unique Values Observed rule block, LogRhythm Axon now covers 90% of analytics rules that are imperative to run a SOC. With the Unique Values Observed rule block, LogRhythm Axon looks for the number of the unique values of a specific field within the specified timeframe and will automatically create detections and pull in logs related to those detections. LogRhythm Axon’s analytics rule builder is a quick way to build out complex rules with increased accuracy and low manual effort thus increasing analyst efficiency.
We’ve expanded LogRhythm Axon’s detection capabilities into behavior anomaly detections with the use case of improbable travel. We’ve also made it simple to build out this use case in the platform through the unique values observed rule block. You can easily see if a single user has activity for multiple locations where the distance and time between those locations is not feasibly possible. Rather than looking at multiple locations and regions within a certain timeframe, LogRhythm Axon does an intelligent level of calculations to easily surface these anomalies for investigation.
In addition, we are continuously adding out-of-the-box MITRE ATT&CK detections as well as updating existing ones to help analysts gain a quick time to value and understanding of the nature of threats that are being surfaced via observations.
Greater Insight into Data Collection and Increased Collection Capabilities
We’ll always be improving and enhancing collection to help our customers gain comprehensive visibility into their environment. We want to be as transparent as possible, so we’ve developed a straightforward way for customers to be able to know when individual data sources are being collected into LogRhythm Axon. Customers now have better visibility that logs are being reported correctly by showing the last time a collector was active and the last time the log was received.
In addition, our Axon Agent currently supports Ubunto 20 and CentOS 7, but we know many customers need more insight into Linux distributions. This quarter, we are expanding Linux support to include Ubuntu 22 and RedHat 9. And just like every quarter, we are introducing new log source capabilities.
It’s been a year of continued innovation with the LogRhythm Axon platform and we are excited to deliver our fifth consecutive quarterly release to the platform, keeping our promise to you. Information and documentation on all these new enhancements can be found in our Release Notes, further enabling our customers to realize the full value of our cloud-native SIEM platform.
To learn more about LogRhythm Axon, read the product data sheet or request more information here.