5 New Features that Streamline Security and Compliance with LogRhythm Axon
Posted by: Corey Garretson
The output of a security and information event management (SIEM) platform is only as good as the data that is feeding into it. “Garbage in, garbage out,” as they say. Clean and contextualized data is the foundation of accurate security…
Read MoreJuly 1, 2024
Expand Log Source Collection and Flexibility with LogRhythm 7.17
Posted by: Ryan Gamboa
Behind every LogRhythm product release, our team puts customers at the very core. That’s part of our commitment to you every 90 days. In our ninth consecutive quarterly release, we’ve opened LogRhythm SIEM to allow any JSON agent that supports…
Read MoreJuly 1, 2024
Benefits of JSON Log Source Collection for LogRhythm Customers
Posted by: Jake Haldeman
When it comes to log sources, LogRhythm recognizes there are limitless options. After all, more than 30,000 Softwares as a Service (SaaS) companies exist around the globe. While we can’t keep up with every SaaS tool in the market, LogRhythm…
Read MoreJuly 1, 2024
LogRhythm’s Machine Data Intelligence Fabric Empowers AI-Ready Organizations to Enter the Modern Era with Confidence
LogRhythm, the company helping security teams stop breaches by turning disconnected data and signals into trustworthy insights, today announced its 9th consecutive quarterly release. In the AI-ready world, LogRhythm empowers security teams with the highest integrity data in the security…
Read MoreJuly 1, 2024
How LogRhythm Helps You Comply with NERC CIP-015-01
Posted by: Kyle Dimitt
NERC-CIP aims to secure and manage the security of the Bulk Electric System (BES) in North America. At the request of the Federal Energy Regulatory Commission (FERC), NERC completed an INSM study to analyze the risks associated with a lack…
Read MoreJune 28, 2024
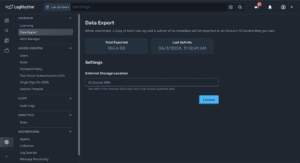
April 2024 Quarterly Launch – LogRhythm Axon
In our April 2024 quarterly release, LogRhythm Axon showcases new enhancements from its two week release cycles. In this webinar, LogRhythm product leaders demo the latest enhancements for LogRhythm Axon including: Import and export of dashboards and searches enables community…
Read MoreApril 24, 2024
April 2024 Quarterly Launch – LogRhythm SIEM
In our April 2024 quarterly release, LogRhythm SIEM introduces new enhancements to bring you faster time to value. In this webinar, LogRhythm product leaders demo the latest enhancements for LogRhythm SIEM including: Introduced cases to be separated based on entities…
Read MoreApril 24, 2024
LogRhythm and RedLegg are Now Delivering Cloud-Native SIEM Capabilities to Security Operations Teams
LogRhythm Axon is Now Available to RedLegg Customers as Part of its Results-Driven Security Offerings LogRhythm, the company helping security teams stop breaches by turning disconnected data and signals into trustworthy insights, today announced its partnership with RedLegg, a master…
Read MoreApril 9, 2024
Secure a Faster Time to Value With LogRhythm Axon
Posted by: Jeff Week
LogRhythm Axon was built from the ground-up so that security teams can focus on the actual job of cybersecurity. With LogRhythm Axon, security teams can immediately realize the value of the platform as they do not have to focus on…
Read MoreApril 1, 2024
Cut Dashboard Noise and Easily Retire Log Sources with LogRhythm 7.16
Posted by: Jake Haldeman
At LogRhythm, we’re focused on making your security journey easier with feature releases every 90 days for our self-hosted security information and event management (SIEM) platform, LogRhythm SIEM. As part of our latest quarterly release, we’re introducing a new feature…
Read MoreApril 1, 2024
LogRhythm Unveils Advanced Capabilities for Cloud-Native SIEM Platform, LogRhythm Axon
LogRhythm’s 8th Quarterly Release Enhances Global Security Communication and Collaboration Recent global research reveals 61% of organizations still rely on manual and time-intensive methods for sharing security status updates. In response, LogRhythm, the company helping security teams stop breaches by…
Read MoreApril 1, 2024
LogRhythm and SOC Prime Announce Partnership to Accelerate Threat Detection and Hunting
New partnership combines LogRhythm Axon’s analytics and threat management with SOC Prime’s cutting-edge capabilities LogRhythm, the company helping security teams stop breaches by turning disconnected data and signals into trustworthy insights, today announced its partnership with SOC Prime, the world’s…
Read MoreMarch 19, 2024
January 2024 Quarterly Launch – LogRhythm Axon
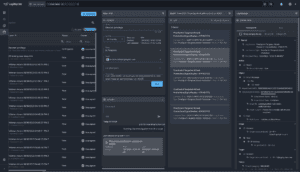
LogRhythm’s January 2024 Quarterly Release introduces new enhancements to bring you faster time to value. In this webinar, our product leaders dive into the latest enhancements to LogRhythm Axon for expanded SaaS-based and cloud-native security, including: New interactive single screen…
Read MoreJanuary 19, 2024
January 2024 Quarterly Launch – LogRhythm SIEM
In our January 2024 quarterly release, LogRhythm SIEM introduces new enhancements to bring you faster time to value. In this webinar, LogRhythm product leaders demo the latest enhancements for LogRhythm SIEM including: New supported log sources and parsing capabilities for…
Read MoreJanuary 19, 2024
Securing Operational Technology in Healthcare — Introducing a New Module
Posted by: Miste Staadt
Current Healthcare Cybersecurity Landscape The global healthcare industry is vastly diverse, encompassing areas such as provider services and managed care, pharmaceuticals and biotechnology, distributors and facilities, along with supplies and equipment. With that, the digital transformation of healthcare data, remote…
Read MoreJanuary 16, 2024
LogRhythm SIEM 7.15: Leverage New Beats and Platform Improvements
Posted by: Ryan Gamboa
Getting data into your security information and event (SIEM) instance is crucial, and LogRhythm is highly focused on making it easy to do that. As part of our latest quarterly product release, LogRhythm SIEM version 7.15 builds on the innovation…
Read MoreJanuary 4, 2024
LogRhythm Product Innovation Prioritizes Speed and Efficiency for Fast, Agile and High-Performing Security Teams
SOC Team Efficiency Bolstered by a New Seamless, Integrated User Experience LogRhythm, the company helping security teams stop breaches by turning disconnected data and signals into trustworthy insights, today announced its 7th consecutive quarterly release. This announcement comes on the…
Read MoreJanuary 4, 2024
Attain Faster and More Accurate Threat Investigation with LogRhythm Axon’s Single Screen Investigation
Posted by: Josh Feldman
When we built our cloud-native security information and event management (SIEM) platform, LogRhythm Axon, our goal was to make the product as efficient as possible to make the life of an analyst easier. With feature releases every two weeks, we’ve…
Read MoreJanuary 4, 2024