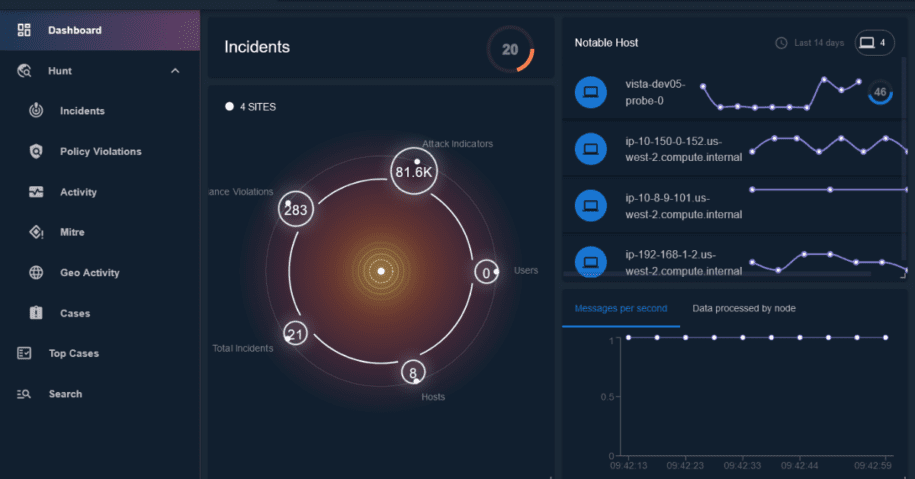
The amount of new network traffic that must be monitored across users and hosts in your environment make the job of an analyst difficult; new network threats appear every day and it is easy to get lost in all the noise when trying to monitor, surface, and detect threats. LogRhythm is making it even easier for customers to detect network threats with our network detection and response (NDR) solution.
With our January LogRhythm NDR release, we listened to customer feedback and focused on the ability to ingest more data that can be easily processed to gain greater visibility into detecting threats on your network. In addition, we continued our commitment to enhance the analyst experience by moving to our new user interface (UI). Read on to learn more about our newest LogRhythm NDR features and network threat detection capabilities.
More data ingestion for greater visibility
LogRhythm NDR collects data from many sources including endpoint detection and response (EDR) tools. Adding to our current integration with the primary EDR vendors – Carbon Black, Cyberreason, Crowdstrike, SentinalOne, Cisco Secure Endpoint, and Sophos – LogRhythm NDR expanded its integrations with the ability to ingest data from Microsoft EDR (Windows Defender). This feature expands your security operations center (SOC) visibility by giving you greater awareness about the potential endpoint threats in your network and the ability to detect and respond to them.
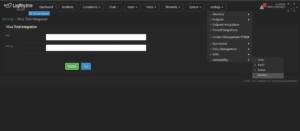
In addition to expanding data collection from new EDR solutions, we wanted to make it easy to ingest data from VirusTotal. With the newly released VirusTotal configuration page, you can now link NDR to VirusTotal directly by collecting API URL and Token. This will enable NDR to collect data about domain resources, URL resources, and IP resources from VirusTotal. This added method of data collection gives more visibility and optimizes network threat detection to secure your environment.
Enhance the analyst experience
We know how critical the analyst experience is. That is why our team dedicated resources to help ease the analyst workflow by introducing a new and refreshed user interface in October. With the latest LogRhythm NDR release, we continued to roll out updates to our pages to help you respond quicker and do your job more efficiently.
For example, administrative workflows in the Settings and System pages are now available in the new UI. These spaces will help NDR administrators perform tasks like monitoring the Probe Node status and deploying and managing third-party integrations. Our Users and Hosts pages are also now available. These pages help customers understand the current state of anomalous activity as it relates to these entities in their environment.
Here is the former UI:
Here are our latest updates to the interface:
That is not all. We are continuing to move all our pages and functionality to the new UI. If you are a current customer, you can get acquainted with the new UI in the LogRhythm NDR product by clicking on the blue “NEW BETA UI” button in the top right corner of the NDR interface.
Our latest LogRhythm NDR release is just the beginning of more exciting things to come to address your network threat detection needs. For additional information about LogRhythm NDR, read the data sheet or schedule a demo.