6 Ways to Crush Your Tech Internship
Congratulations on landing the internship! Since you are reading this post, I’m assuming you’re now in the broad and intimidating space of technology — be it software or website service, welcome! Your tech industry internship will be challenging and rewarding.…
Read More
April 15, 2020
Three Takeaways from the 2020 SANS Women in Security Survey
About the SANS 2020 Women in Security Survey Women may only represent about 20 percent of the cybersecurity workforce as of 2019[1], but when it comes to leveling the playing field, this number is up from 11 percent since 2013.…
Read More
April 14, 2020
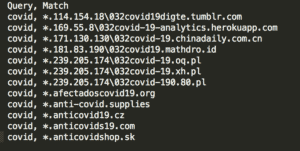
Detecting Young Domains with Palo Alto Networks and LogRhythm
Posted by: Brian Coulson
As the world continues dealing with a pandemic involving the coronavirus disease (COVID-19), malicious campaigns are well underway. For example, an opportunistic attacker will leverage a user’s sense of urgency and curiosity to prompt them to open a malicious email,…
Read More
April 9, 2020
Automate Amazon S3 Provisioning for Healthcare Compliance with SOAR
Cloud storage instances like Amazon Simple Storage Service, Amazon S3, have made it easier than ever before for healthcare professionals to access and share valuable patient data. While these advancements have improved customer care across providers, configuring access policies, provisioning…
Read More
April 8, 2020
Using Open-Source Intelligence to Detect Attacks Using Newly Created Domain Names
Posted by: LogRhythm Labs
When high-profile threats surface, they are often accompanied by a flurry of information sharing from security researchers and practitioners. The information they share can be delivered in a variety of formats. For example, following the recent malware activity surrounding the…
Read More
April 1, 2020
Detect Phishing Campaigns and Stolen Credentials with Custom AI Engine Rules
Posted by: LogRhythm Labs
Attackers have been known to take advantage of world events to increase their use of phishing, social engineering, malware delivery, and numerous other nefarious attacks. The recent COVID-19 pandemic is no exception as attackers are currently creating custom campaigns to…
Read More
March 31, 2020