Breaking Down the Anatomy of a Phishing Attack
Anatomy of a Phishing Attack Detecting a spear phishing attack can often be like searching for a needle in haystack. However, your security operation center (SOC) analysts can use LogRhythm’s SmartResponse™ and AI Engine to rapidly detect and respond to…
Read More
August 23, 2017
Mamba Ransomware Analysis
Posted by: LogRhythm Labs
Mamba Ransomware Background In September of 2016, a strain of ransomware was found in the wild which performed full disk encryption. According to Kaspersky Lab researchers1, this ransomware strain named “Mamba” now appears to be re-circulating, primarily in Brazil and…
Read More
August 15, 2017
First Financial Bank Unifies Threat Data and Streamlines Response
LogRhythm Enables Comprehensive Visibility and Enhanced Incident Workflows When Michael Cole took on his new role as Chief Information Security Officer at First Financial Bank (NASDAQ:FFIN), he inherited a fragmented security operations program that provided a limited visibility into the…
Read More
August 15, 2017
Three Weeks Left to Enter the Rule Your Network Challenge
There are only three weeks left to enter the Rule Your Network to win up to $18,000 USD. Submit an entry by August 31st and you’ll be eligible to win our cash prizes. How to Enter To start, download NetMon…
Read More
August 8, 2017
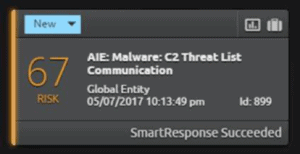
How to Make Your SIEM Speak
Your security teams can be responsible for managing a number of logs, so how do you make malicious behavior and alerts stand out? Using LogRhythm’s SmartResponse™, you can make your SIEM speak to you and audibly alert to a threat.…
Read More
August 8, 2017
Build a Highly Efficient SOC—Even with Limited Resources
Security Teams are Overwhelmed If your team is struggling to keep up and getting bogged down by manual processes, it may feel like you will never be one step ahead of cyberthreats that may threaten your business. In a perfect…
Read More
August 1, 2017