Deepen Your Remote Desktop Protocol Visibility with Log Sources
Remote desktop is a common feature in operating systems. It allows a user to connect to a computer in another location and interact with the desktop remotely. Microsoft implemented this capability via its Remote Desktop Protocol (RDP) for Windows desktop…
Read MoreApril 24, 2020
What DoD Contractors Need to Know About the New Cybersecurity Maturity Model Certification
Posted by: Kyle Dimitt
The Cybersecurity Maturity Model Certification (CMMC) is a new requirement from the U.S. Department of Defense (DoD). It mandates that DoD contractors obtain third-party certification to ensure appropriate levels of cybersecurity practices are in place to meet “basic cyber hygiene,”…
Read MoreApril 22, 2020
Monitor Zoom Security and Privacy Risks Using the LogRhythm NextGen SIEM
Posted by: Andrew Hollister
The mass migration to remote working in recent times has caused an increased focus on the security of remote collaboration tools. LogRhythm has found a variety of these tools in our customer base and has built collection methods and analytics…
Read MoreApril 21, 2020
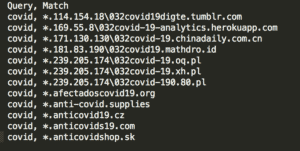
Detecting Young Domains with Palo Alto Networks and LogRhythm
Posted by: Brian Coulson
As the world continues dealing with a pandemic involving the coronavirus disease (COVID-19), malicious campaigns are well underway. For example, an opportunistic attacker will leverage a user’s sense of urgency and curiosity to prompt them to open a malicious email,…
Read MoreApril 9, 2020
Using Open-Source Intelligence to Detect Attacks Using Newly Created Domain Names
Posted by: LogRhythm Labs
When high-profile threats surface, they are often accompanied by a flurry of information sharing from security researchers and practitioners. The information they share can be delivered in a variety of formats. For example, following the recent malware activity surrounding the…
Read MoreApril 1, 2020
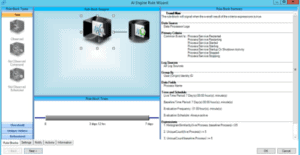
Detect Phishing Campaigns and Stolen Credentials with Custom AI Engine Rules
Posted by: LogRhythm Labs
Attackers have been known to take advantage of world events to increase their use of phishing, social engineering, malware delivery, and numerous other nefarious attacks. The recent COVID-19 pandemic is no exception as attackers are currently creating custom campaigns to…
Read MoreMarch 31, 2020
Insights and Included Content to Protect Your Organization During Times of Crisis
Posted by: LogRhythm Labs
In times of crisis and uncertainty, nefarious threat actors have always preyed on the public and worked to exploit the situation for their benefit. The COVID-19 pandemic is no exception, as attackers have begun to masquerade and disguise common cyberattacks…
Read MoreMarch 27, 2020
Living Off the Land Attacks with Scheduled Task
Posted by: Brian Coulson
In our previous living off the land (LotL) blog post, we discussed why attackers use tools that already exist in the environment to plan an attack. But what role does Microsoft Scheduled Tasks in an attacker’s plan? In this post, we’re…
Read MoreMarch 10, 2020
LogRhythm Labs: Cybersecurity Expertise Delivered into Your LogRhythm Deployment
Posted by: Andrew Hollister
What is LogRhythm Labs? LogRhythm Labs is the team that researches and creates the content that goes into the LogRhythm NextGen SIEM Platform. The team mission is to: Research and deliver world-class security, compliance, intelligence, and operational risk content to protect our customers…
Read MoreMarch 10, 2020
4 Trending Phishing Techniques: Real-Life Examples and Tips for Detection
Many successful attacks begin with a phishing email that some user falls for. And that’s why MITRE prominently features Spearphishing (T1192) as an Initial Access technique in ATT&CK. View the on-demand webinar with Ultimate Windows Security to learn about the latest phishing techniques used by attackers and how MITRE ATT&CK can help detect and remediate these threats.
Read MoreMarch 9, 2020
Beware of Coronavirus Phishing Attempts — Tips to Keep Your Organization Safe
Coronavirus: it’s what every news outlet and person is talking about. With the outbreak of the infection, people want to stay up to date on the latest news and reports, so they’re looking up data and clicking on links to…
Read MoreMarch 9, 2020
2019 in the Rearview, 2020 in the Windshield
Posted by: Andrew Hollister
2019 was a big year for IT security whichever way you choose to look at it. Huge volumes of records were exposed, loads of organizations experienced a ransomware attack, skimmers compromised countless websites, and European authorities issued massive fines under…
Read MoreFebruary 5, 2020
8 Cybersecurity Predictions for 2020
Posted by: LogRhythm Labs
As we do each year, the LogRhythm Labs team came together recently to reflect on the year in cybersecurity and think about what’s to come. 2019 was definitely interesting. Breaches continued to keep organizations on their toes, with over 5,000…
Read MoreDecember 11, 2019
Examining the baseStriker Vulnerability
Posted by: Eric Brown
The zero-day “baseStriker” vulnerability is still widely in use, but do you know what to look out for if it finds its way into your organization? While 18 months have passed since Microsoft developed a fix for the vulnerability that…
Read MoreNovember 14, 2019
Experts Weigh in on National Cybersecurity Awareness Program
In honor of National Cybersecurity Awareness Month, we sat down with some of our security experts to talk about their experience raising awareness in the industry and implementing cyber training. Read the interview to get their thoughts and some inspiration…
Read MoreOctober 28, 2019
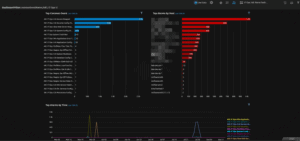
Exploring IT Operations with LogRhythm
Posted by: Julian Crowley
The LogRhythm NextGen SIEM Platform collects, classifies, and normalizes log data from over 800 unique source types. At LogRhythm, our focus has always been on identifying and mitigating security threats through monitoring, alarming, and event log correlation. And while we…
Read MoreAugust 30, 2019
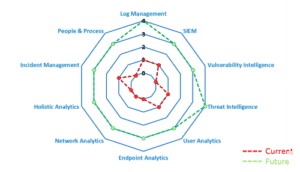
How to Balance Security Maturity and Compliance with LogRhythm
Compliance doesn’t guarantee prevention against a breach, and it never will. Various frameworks, legislation, and regulations are meant to lay part of the foundation for organizations to build and expand on; though this rarely is the case. While different industries…
Read MoreApril 22, 2019
Aligning the LogRhythm NextGen SIEM Platform with the MITRE ATT&CK Framework
Posted by: LogRhythm Labs
Contributors to this blog include Dan Kaiser and Brian Coulson. The MITRE ATT&CK framework is quickly becoming a focal point in the security world — and for good reason. This framework provides a consistent, industry-wide standard on which you can…
Read MoreApril 15, 2019