Your analysts are efficient. They are creative problem solvers who prefer to spend their time putting those inventive skills to use rather than expending energy on mundane tasks. For example, logging into an active directory and unlocking a user account 15 times is a monotonous activity — and not an efficient allocation of your team’s time and skills.
Most analysts will naturally look for ways to automate these kinds of tasks to focus on more pressing and challenging projects at hand. SIEM platforms like LogRhythm give analysts the SOC automation tools they need to easily automate everyday workflows, processes, and activities so they can make the most of their time and resources.
Detecting Cyberthreats Faster with Automated Threat Detection and Response
When fighting cyberthreats, you need to be as efficient as possible. SOC automation tools reduce your time to qualify (TTQ) and mean time to respond (MTTR) to a threat. TTQ refers to the average time it takes to determine whether an incident is benign or should be considered a threat that requires investigation. MTTR denotes the average time it takes your system to return to normal operations and prevent a breach from spreading.
SOC automation tools help your team remove the “wait time” (the time it takes for a human to perform an action that could be executed by your SIEM). Examples of activities that can be automated include typing in a command, logging into a different system to perform an action, or gathering supporting information.
When responding to a threat, time is of the essence. In 2020, it took organizations an average of 280 days to identify and contain a data breach. Minutes can mean the difference between a contained incident and a damaging breach. Your analysts need to save time wherever they can and prioritize the tasks that require their skillset.
LogRhythm’s embedded security orchestration, automation, and response (SOAR) capabilities can help automate steps within your team’s current process without bolting on another tool or learning a new interface.
How LogRhythm SOAR Helps Automate Everyday Security Operations
When a threat breaches your network, your team will need to follow a series of steps to ensure successful containment, beginning with the initial collection of data and ending with your network’s recovery. You can find further details about this progression in the Threat Lifecycle Management (TLM) framework. Each stage of the TLM framework requires analysts to take different actions, and therefore, it introduces new opportunities for automation.

LogRhythm SOAR expedites workflow across the entire TLM framework — meaning you can automate workflows throughout the entire threat qualification and response process. Employing LogRhythm SOAR makes your team’s job easier and more effective.
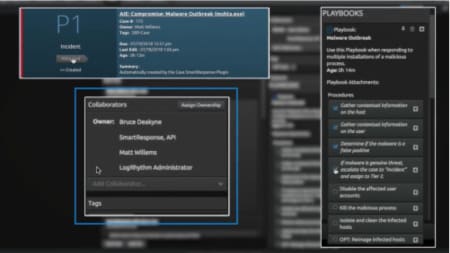
Figure 2: LogRhythm playbooks offer guided workflows and easier team collaboration
LogRhythm SOAR enables your team to quickly detect and respond to an incident through guided case workflow, improved collaboration capabilities, and automation. An effective SIEM delivers as much information as possible to analysts when an alarm fires, so they can spend less time gathering information and more time focusing on containing the threat. LogRhythm SmartResponse™ automation does just that by automating many everyday tasks, including the gathering of information.
SmartResponse automation can be used to:
- Notify analysts of high-priority alarms through various channels
- Automate collection of contextual information from outside systems
- Rapidly contain a breach fully automated or through approval workflow
Getting Started with LogRhythm SmartResponse Automation
Customers have access to an extensive library of prebuilt SmartResponse automation plugins. LogRhythm also helps users modify existing plugins or create custom plugins using their preferred programming/scripting technology, such as Bash, Perl, PowerShell, or Python. You can test custom plugins with an integrated tool that documents output and identifies errors.
The beauty of SmartResponse automation plugins is that they put you in control, allowing you to customize the automation of your SOC. Learn more about how you can use SmartResponse automation to enable automation in this blog.
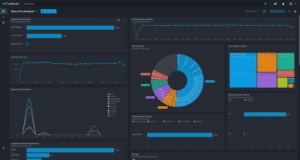
Allocate Resources with Case Management and Full Spectrum Analytics
It’s important for a SOC manager to identify areas in which the security team excels, as well as areas to improve. LogRhythm offers full spectrum analytics that deliver actionable insights, so you can identify specific steps and processes along the TLM workflow that take your team more time to perform. SOC managers can then allocate additional resources to processes that prove more difficult for their time and, ultimately, expedite threat detection.
Case Management provides the metrics you need to measure SOC performance and success. It serves as a collaboration tool between your analysts to ensure that investigation and remediation are complete — without duplicating efforts across team members. Case Playbooks help SOC workflows to be consistent and repeatable by ensuring individuals are using the same investigation and incident response methodology.
By making workflows consistent, it’s easier to predict capacity and find places to improve, such as Agile software development, for example. Case Management also gives the SOC a repository for historical work. Your team can save time in future investigations with visibility into which hosts or users were investigated in the past and the outcome of that investigation.
Case Management trends and visualizes performance indicators, such as TTQ and MTTR. You can utilize LogRhythm Case Management to find patterns in your threat response process, gain actionable insights, and apply lessons learned to expedite threat detection. With customized performance metrics, you can fully understand your team’s capabilities and better allocate your resources. You can also use Case Metrics to demonstrate your team’s performance to upper-level management, ensuring security buy-in from the C-suite.
Learn more about ways to incorporate SOC automation tools into your business in the LogRhythm Community.