LogRhythm’s Hackathon Sparks New Innovation
Posted by: Kish Dill
Twice a year, the LogRhythm Research and Development team hosts an internal hackathon event to give our engineers an opportunity to collaborate, share innovative projects, and get awarded for their ideas. Past and present hackathon projects have inspired Product and…
Read MoreMay 27, 2022
Threat Intelligence Platforms and LogRhythm
Read MoreApril 26, 2021
What SOC Automation Tools Can Do for Your Team
Posted by: Matt Willems
Your analysts are efficient. They are creative problem solvers who prefer to spend their time putting those inventive skills to use rather than expending energy on mundane tasks. For example, logging into an active directory and unlocking a user account…
Read MoreSeptember 28, 2020
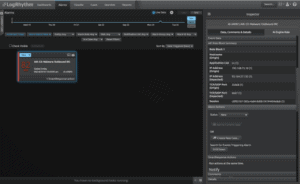
Rapidly Qualify and Triage Alarms with Contextual SmartResponse Automation
Posted by: Matt Willems
Alarms don’t fire when it’s convenient. You could be threat hunting, out to lunch, or even in bed at 4 a.m. when an alarm comes your way. No matter where you are, you’ll need to quickly determine the severity of…
Read MoreOctober 7, 2019
Notifying and Collaborating with LogRhythm SmartResponse Automation
Posted by: Matt Willems
When a threat emerges in your environment, you need to investigate it as soon as possible to keep it from incurring damage. For that to happen, you need to be notified that it exists in the first place. A typical…
Read MoreSeptember 5, 2019
Introducing LogRhythm Echo
LogRhythm Echo is now available. LogRhythm Echo is a standalone app that simulates incident scenarios for demonstration purposes, allowing you to test security rules, verify embedded content, and perform red team preparedness exercises. Regardless of the size of your team,…
Read MoreJuly 24, 2019
R&D Considerations for Developing a Big Data Product
Big data — it’s all the rage in the technology industry right now, and for good reason. Data holds information that, if analyzed properly, reveal invaluable insights that you can use for just about anything — from streamlining internal processes…
Read MoreDecember 10, 2018
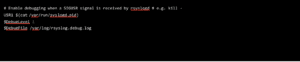
Troubleshooting Delayed Syslog Messages
Posted by: Jeffrey Braucher
Anytime our team has been involved in a system migration, there has always been someone who claimed the new system was slower than the old one. In a recent case, the team had just completed the migration of a computing…
Read MoreNovember 16, 2018
Creating and Managing Playbooks with LogRhythm APIs
New to LogRhythm 7.4: Playbooks Feature Set Standard procedures have been a cornerstone of security best practice since their invention. You may call them runbooks, standing procedures, checklists, or playbooks. Either way, you likely have one or more collections of…
Read MoreOctober 29, 2018
Automate Common Threat Hunting and Response Actions with SmartResponse
Posted by: Matt Willems
When your team detects a threat, rapid qualification and response can mean the difference between quick containment and a breach of critical data. Relying solely on manual processes puts your organization at risk. To reduce response time, you should automate…
Read MoreOctober 2, 2018
Recognize Indicators of Compromise with Complete Endpoint Visibility
Posted by: Matt Willems
As attacks increase in breadth, scope, and complexity, one of the most common vectors that remains is the endpoint. With up to thousands of endpoints to safeguard, it’s imperative to have solutions that seamlessly integrate to provide complete visibility into…
Read MoreAugust 28, 2018
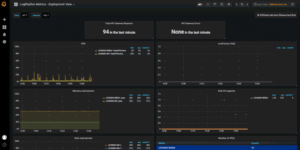
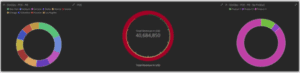
Measure and Optimize SOC Performance with New LogRhythm Tools
Posted by: Matt Willems
When faced with a bombardment of threats and a severe resource shortage, the best way to keep your organization ahead of a damaging attack is to make the most of what you have. You need your team and tools to…
Read MoreAugust 8, 2018
Enrich Your Security Data with LogRhythm and Kibana
Data is a powerful tool. But storing, organizing, and adding value to it to enable better decisions can be difficult. Most companies strive to find a way to best preserve all of their data, and then use that data to…
Read MoreJuly 17, 2018
IT Security in an OT World
Before we had the Internet of Things (IoT), ubiquitous wireless access, high speed data pipes, or even core internet protocols including HTTP and TCP, we had industrial automation. Operational Technology (OT) is the latest umbrella term to encompass functionalities such…
Read MoreJanuary 24, 2018