Ensure Your Systems Are Patched from Meltdown and Spectre Vulnerabilities
Posted by: LogRhythm Labs
Contributors to this blog include Nathaniel Quist and Dan Kaiser. Last week, we provided background on Spectre and Meltdown vulnerabilities in our LogRhythm Labs Security Advisory on Spectre and Meltdown blog. In response to these vulnerabilities, LogRhythm Labs has developed…
Read MoreJanuary 11, 2018
Security Advisory: Meltdown and Spectre Vulnerabilities
Posted by: LogRhythm Labs
Between January 3 and 4, 2018, three vulnerabilities in processor hardware were made public that affect nearly all modern architectures. Impacted architectures include Intel, AMD, and ARM. If successfully exploited, an unprivileged process on an affected system could read privileged…
Read MoreJanuary 5, 2018
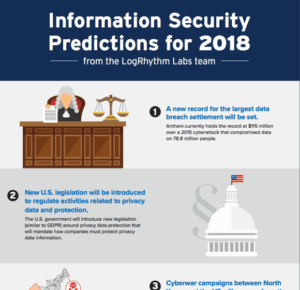
8 Information Security Predictions for 2018
Posted by: LogRhythm Labs
2017 has been another year full of front-page computer security events and incidents. Headlines have bulged with state-sponsored attacks, ransomware, leaks, and a continuing wave of data breaches. As we welcome 2018, we’ve not only reflected on the cyberattacks of…
Read MoreJanuary 2, 2018
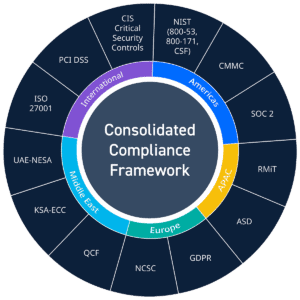
One Compliance Module to Rule Them All: Consolidated Compliance Framework
Posted by: LogRhythm Labs
The continued growth, proliferation, and awareness of cybersecurity as a necessary focus for all companies has helped revolutionize the global compliance landscape. A growing number of old regulations have been re-factored to include more stringent cybersecurity controls. New regulations are…
Read MoreDecember 13, 2017
Information Security Predictions for 2017 – How Did We Do?
Posted by: LogRhythm Labs
Around this time every year, we dust off our crystal ball, pull out the casting runes, and ruminate over what might happen in the world of Information Security in the year to come. While we are gathering information for our…
Read MoreDecember 6, 2017
Phishing Intelligence Engine (PIE): Open-Source Release
We are pleased to announce the release of the LogRhythm Phishing Intelligence Engine (PIE), an integrated app with LogRhythm’s NextGen SIEM Platform. What is Phishing Intelligence Engine (PIE)? LogRhythm’s PIE can help streamline and automate the entire process of tracking,…
Read MoreNovember 8, 2017
Bad Rabbit Ransomware Technical Analysis
Posted by: LogRhythm Labs
Update: Further analysis of the code revealed new information regarding the spread of Bad Rabbit across the network. This post has been updated to reflect this new information. Bad Rabbit Ransomware Background On the afternoon of October 24, 2017 (BST),…
Read MoreOctober 27, 2017
The Reality of Ransomware
As the ransomware landscape continues to quickly change and evolve, every CISO also needs to evolve their business continuity and disaster recovery plans to ensure the impacts of ransomware can be minimized. If you haven’t updated your business continuity and…
Read MoreSeptember 18, 2017
What is the GDPR and How Can You Prepare?
The General Data Protection Regulation (GDPR) is the world’s first attempt at implementing big data compliance regulation, and it seems to be inspiring some fear throughout the compliance industry. Now that GDPR has come to combat the uptick in cyberattacks,…
Read MoreSeptember 7, 2017
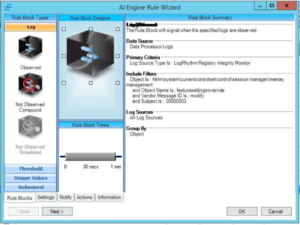
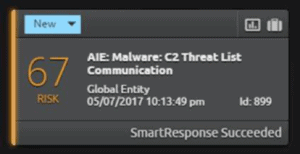
Breaking Down the Anatomy of a Phishing Attack
Anatomy of a Phishing Attack Detecting a spear phishing attack can often be like searching for a needle in haystack. However, your security operation center (SOC) analysts can use LogRhythm’s SmartResponse™ and AI Engine to rapidly detect and respond to…
Read MoreAugust 23, 2017
Mamba Ransomware Analysis
Posted by: LogRhythm Labs
Mamba Ransomware Background In September of 2016, a strain of ransomware was found in the wild which performed full disk encryption. According to Kaspersky Lab researchers1, this ransomware strain named “Mamba” now appears to be re-circulating, primarily in Brazil and…
Read MoreAugust 15, 2017
How to Make Your SIEM Speak
Your security teams can be responsible for managing a number of logs, so how do you make malicious behavior and alerts stand out? Using LogRhythm’s SmartResponse™, you can make your SIEM speak to you and audibly alert to a threat.…
Read MoreAugust 8, 2017
Identifying PowerShell Tunneling Through ICMP
Hackers are constantly looking for ways to bypass traditional network defenses, and exploiting the Internet Control Message Protocol (ICMP) as a covert channel for a reverse shell is a commonly used method for attack. However, you can use LogRhythm’s NetMon…
Read MoreJuly 26, 2017
Analyzing ICMP Traffic with NetMon
The Internet Control Message Protocol (ICMP) is one of the foundational internet protocols that define how systems talk to each other. Commands such as ping and traceroute are supported by ICMP. Based on request for comments (RFC) 792, ICMP has…
Read MoreJuly 26, 2017
Automate Project Management with SmartResponse
The SIEM is a great central aggregate for case data and analytics, but also has the ability to give your team back valuable time if you take advantage of automation. The more automation you can build into a SIEM, the…
Read MoreJuly 20, 2017
Using the Internet of Things and SmartResponse to Receive SIEM Alarms
Wouldn’t it be great if you could be notified of SIEM alarms through the Internet of Things (IoT)? Well, now you can! Introducing the Philips Hue SmartResponse™ and PowerShell script. Imagine that your analysts are busy working on other things,…
Read MoreJuly 6, 2017
NotPetya Technical Analysis
In our Detecting Petya/NotPetya post, we described the way in which NotPetya (or “Nyetna” as it has also been named) spreads to other systems on the network without use of the ETERNALBLUE/ETERNALROMANCE SMBv1 exploits. (Although the code contains the ability…
Read MoreJune 30, 2017
Deploying NetMon Freemium at Home to Monitor IoT Devices
Why Monitor IoT Devices at Home? LogRhythm’s NetMon Freemium is a powerful and easy-to-use product, so why not fully realize its potential both at home and in the office? In-home Internet of Things (IoT) devices, such as sensors, lights, cameras,…
Read MoreJune 29, 2017